Web Security Audits: Why Every Business Website Needs Regular Checks
Table of Contents
Web security audits are one of the most overlooked elements of running a business online. Most organisations invest time and money into building a website, then leave it largely unattended from a security standpoint. That is a significant risk. Web security audits give you a structured way to identify vulnerabilities before attackers find them, and they are as important for a small Belfast retailer as they are for a large enterprise.
At ProfileTree, our digital team works with businesses across Northern Ireland, Ireland, and the UK on web design, SEO, content, and digital strategy. Security is not an afterthought in that work; it is built into how we approach every project. Web security audits form a core part of any responsible website management process, and this guide explains exactly what they involve, why they matter, and how to put them into practice.
Whether you run a WordPress site, an e-commerce store, or a corporate web platform, the case for regular web security audits is straightforward: the cost of a breach is almost always far greater than the cost of prevention.
What Are Web Security Audits?
Web security audits are structured examinations of a website’s technical setup, configurations, access controls, and third-party components. The goal is to identify weaknesses that could be exploited by attackers, whether those weaknesses sit in the code, the server settings, the plugins, or the policies governing how the site is managed.
A well-run audit goes beyond running an automated scanner. It involves reviewing how the site handles user data, how authentication works, whether sensitive files are exposed, and whether the site meets current regulatory requirements. Web security audits also look at how updates are managed, since outdated software is one of the most common entry points for attacks.
Why Regular Web Security Audits Matter
The threat landscape changes constantly. A configuration that was secure 18 months ago may now carry known vulnerabilities. Web security audits are not a one-time task; they are an ongoing part of responsible website ownership. For businesses that handle customer data, take payments, or operate under regulated industries, they are also a compliance necessity.
As Ciaran Connolly, founder of ProfileTree, puts it: “In our digital-first world, a website’s security is as crucial as its content and design. Regular web security audits are not just recommended; they’re a necessary business practice for any company that wants to protect its reputation and its customers.”
Businesses that invest in website security management and regular updates as part of their hosting arrangement are far better placed to respond quickly when vulnerabilities emerge. Web security audits help you:
- Identify vulnerabilities before they are exploited
- Maintain compliance with UK-GDPR and relevant industry regulations
- Protect customer data and avoid costly breach notifications
- Preserve search rankings, since Google penalises compromised sites
- Maintain the trust of customers and partners
Common Vulnerabilities Web Security Audits Uncover
Web security audits tend to surface a predictable set of problems, particularly for sites that have not been reviewed in some time. Understanding what auditors look for helps you prioritise where to focus attention first.
SQL Injection and Cross-Site Scripting
These two attack types remain the most common entry points for attackers on business websites. SQL injection involves manipulating database queries through form inputs or URL parameters, potentially giving an attacker access to your entire database. Cross-site scripting (XSS) allows attackers to inject malicious scripts into pages viewed by other users, often to steal session cookies or redirect visitors.
Web security audits test for both by simulating attack conditions in a controlled environment. If your site processes user input anywhere, such as contact forms, search fields, or login pages, these tests are essential. According to the OWASP Top Ten, injection flaws and broken access controls have consistently ranked among the most critical web application security risks for over a decade.
Broken Authentication and Access Controls
Weak or improperly configured authentication is consistently flagged in web security audits. This includes default admin credentials that have never been changed, accounts with excessive permissions, and login systems that do not enforce rate limiting or multi-factor authentication. Access control failures allow attackers to view or modify data they should not be able to reach.
Stephen McClelland, Digital Strategist at ProfileTree, notes: “A regularly updated password is your first line of defence against security breaches, but it needs to be paired with proper role management and access reviews to be truly effective.”
Outdated Software and Unpatched Components
Web security audits consistently find outdated CMS versions, themes, and plugins. Each unpatched component is a potential entry point. This is one reason why professional website development should include a clear maintenance and update protocol from day one. Keeping software current closes off more attack vectors than almost any other single action.
Misconfigured Server Settings
Server configuration issues are harder to spot without a structured review. Web security audits examine file permissions, exposed directory listings, error messages that reveal sensitive information, and HTTP security headers that are missing or incorrectly set. These problems are often invisible in day-to-day use but create real exposure.
What a Structured Audit Covers
A thorough set of web security audits addresses all of the following areas:
| Audit Area | What Is Checked | Risk If Missed |
|---|---|---|
| Authentication | Password policies, MFA, session management | Unauthorised account access |
| Input Validation | Forms, search, login fields | SQL injection, XSS attacks |
| Server Configuration | Headers, permissions, error handling | Data exposure, privilege escalation |
| Third-Party Components | Plugins, themes, integrations | Known vulnerability exploitation |
| SSL and Encryption | Certificate validity, HTTPS enforcement | Data interception, trust loss |
| Data Handling | Storage, processing, transmission | UK-GDPR breaches, regulatory fines |
Running a Web Security Audit: Step-by-Step

Understanding what goes into web security audits helps you either carry them out effectively in-house or brief an external team properly. The process is not simply about running a tool and reviewing the output; it requires a structured methodology and clear documentation.
Step 1: Define Scope and Objectives
Before any testing begins, web security audits require a clear scope. Which systems are in scope? Which user roles will be tested? What is the acceptable level of disruption? Setting these boundaries prevents both under-testing and over-testing.
Step 2: Automated Scanning
Tools such as OWASP ZAP and Nessus are widely used for automated vulnerability scanning. They identify common weaknesses quickly and provide a baseline for deeper investigation. Web security audits typically begin with automated scanning to catalogue the attack surface, but automated tools alone are not sufficient. They miss logical flaws, business logic vulnerabilities, and configuration issues that require human review.
Step 3: Manual Penetration Testing
Manual penetration testing simulates how a real attacker would approach your site. This involves attempting to exploit identified vulnerabilities, testing authentication flows, probing for privilege escalation, and reviewing how the application handles unexpected inputs. Web security audits that include manual testing give you a far more accurate picture of real-world risk.
Step 4: Review Policies and Procedures
Technical testing is only part of the picture. Web security audits should also review the policies that govern how your site is managed. Businesses with a clear digital strategy are better placed to define governance frameworks, assign ownership of security tasks, and maintain audit trails. Who has administrative access? How are software updates handled? What is the process when a vulnerability is discovered?
Step 5: Reporting and Remediation
The output of web security audits should be a detailed report that categorises vulnerabilities by severity and recommends specific remediation steps. Vulnerabilities are typically classified as critical, high, medium, or low priority. Critical and high-severity issues should be addressed immediately; medium and low issues should be scheduled into the standard development workflow.
How Often Should You Run Web Security Audits?
For most business websites, web security audits should be conducted at minimum quarterly. Organisations handling payment data, health information, or large volumes of personal data should consider monthly reviews or continuous monitoring. Web security audits should also be triggered by significant site changes, such as new feature launches, platform migrations, or after any known security incident.
Regulatory Compliance and UK-GDPR

Web security audits are not only a technical best practice; for many UK businesses, they are a compliance obligation. The UK General Data Protection Regulation (UK-GDPR) requires organisations to implement appropriate technical and organisational measures to protect personal data. Regular web security audits are one of the clearest ways to demonstrate that obligation is being taken seriously.
What UK-GDPR Requires
Under UK-GDPR, organisations must assess the risk to individuals arising from the processing of their data and implement security measures proportionate to that risk. Web security audits help you fulfil several specific requirements:
- Article 32: Technical measures to ensure data security, including encryption and ongoing confidentiality, integrity, and availability of systems
- Article 25: Data protection by design and by default, which requires security to be built into systems from the outset
- Article 33: Notification of a personal data breach to the ICO within 72 hours of becoming aware of it
Regular web security audits help you demonstrate compliance in the event of an investigation and, more practically, reduce the likelihood of a breach occurring in the first place.
Industry-Specific Compliance
Beyond UK-GDPR, certain industries carry additional requirements. Financial services firms operating under FCA supervision, healthcare providers handling NHS or patient data, and organisations processing payment card data under PCI DSS all face specific security standards. Web security audits should be scoped to include these frameworks where relevant.
Data Residency and Post-Brexit Considerations
UK businesses working with international tools and platforms should verify where their data is stored and processed. Post-Brexit, UK-GDPR operates independently of EU-GDPR, which has implications for data transfers between the UK and EU member states. Web security audits that include a data mapping exercise help clarify these flows and identify transfer mechanisms that need to be reviewed.
Web Security for WordPress and CMS Platforms
The majority of business websites in the UK run on a content management system, with WordPress accounting for a significant share. WordPress is a well-maintained platform with a large security community, but its popularity also makes it a frequent target. Whether you commissioned professional web design or built the site in-house, web security audits for WordPress sites need to cover both the platform and the ecosystem of plugins, themes, and integrations that surround it.
WordPress-Specific Security Checks
Web security audits for WordPress should cover:
- Changing default admin usernames away from ‘admin’
- Using complex, unique passwords and enabling two-factor authentication for all admin accounts
- Keeping WordPress core, themes, and all plugins updated to their latest versions
- Removing inactive plugins and themes, which can still carry vulnerabilities even when deactivated
- Reviewing user roles to ensure contributors, editors, and administrators have only the access they need
- Configuring file permissions correctly to prevent unauthorised write access
- Ensuring the wp-config.php file and other sensitive files are not publicly accessible
SSL Certificates and HTTPS
Every business website should serve content over HTTPS. Web security audits always check that SSL certificates are valid, correctly installed, and set to auto-renew. A lapsed certificate not only creates a security gap but also triggers browser warnings that damage visitor trust and can affect search rankings. Ensure all subdomains are covered and that HTTP requests are permanently redirected to HTTPS.
CMS Hardening and Backup Strategy
CMS platforms benefit from specific hardening steps: disabling file editing within the admin area, limiting login attempts, adding security headers at the server level, and implementing a web application firewall. Pair these measures with a reliable automated backup strategy. Businesses that use a managed WordPress hosting and management service typically have these protections built into their service agreement, which reduces the administrative burden on in-house teams.
Strengthening Authentication and Access Controls
Authentication failures account for a significant proportion of successful web attacks. Web security audits place particular emphasis on how sites verify user identity and manage access, because weaknesses here can make every other security measure irrelevant.
Multi-Factor Authentication
Multi-factor authentication (MFA) requires users to provide two or more forms of verification before accessing an account. For any business website with an admin panel, enabling MFA is one of the most effective single steps you can take. Web security audits flag any admin or editor account without MFA as a high-priority risk. Options range from authenticator apps such as Google Authenticator to hardware keys for higher-security environments.
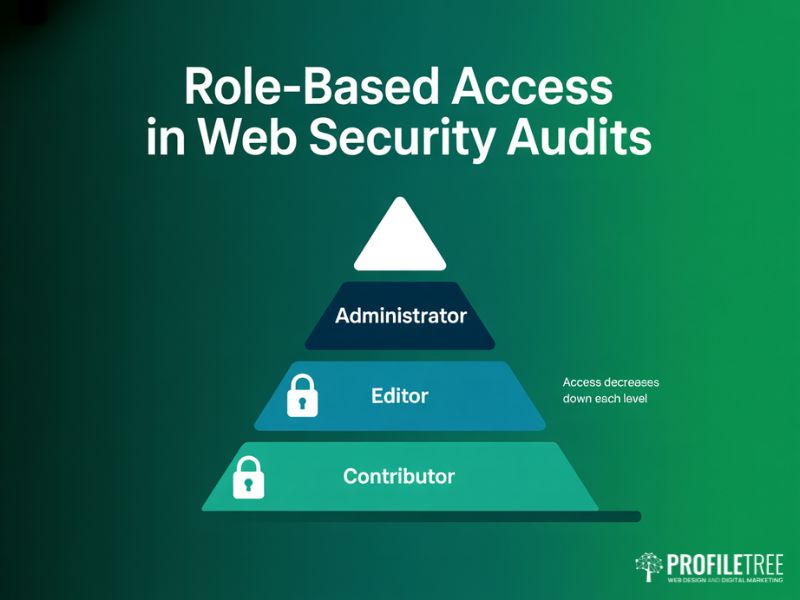
User Role Management
Role-based access control ensures that users can only access what they need to perform their function. Web security audits review the hierarchy of user roles and check whether any accounts carry permissions beyond what their role requires. A content editor does not need database access. A developer account used for a specific project should be deactivated once the work is complete.
| Role | Appropriate Access | What to Restrict |
|---|---|---|
| Administrator | Full site management | Limit to essential personnel only |
| Editor | Content creation and publishing | No access to plugins, settings, or user management |
| Contributor | Draft content submission | Cannot publish without approval |
| Developer (temporary) | Technical access for project scope | Deactivated on project completion |
Building a Continuous Security Programme

A single web security audit gives you a snapshot of your site’s security posture at a point in time. The real value comes from building web security audits into an ongoing programme. Threats evolve, sites change, and new vulnerabilities are discovered in commonly used software.
An ongoing programme built around regular web security audits typically includes quarterly full audits, monthly review of plugin and platform updates with immediate application of critical patches, continuous monitoring via server logs and anomaly alerts, and annual penetration testing by an external specialist for higher-risk environments.
ProfileTree’s approach to web design and digital strategy incorporates security from the project outset. Web security audits sit alongside SEO performance reviews, content updates, and technical health checks as part of how we maintain client sites. A compromised site loses more than data; it can lose its search rankings overnight as Google flags and demotes hacked pages.
Our team also delivers digital training for SMEs through Future Business Academy, where web security audits feature as part of broader training on responsible digital operations. Businesses investing in AI marketing and automation should ensure those platforms and integrations are included in regular web security audits, since AI-powered attack tools are making automated scanning and credential stuffing faster than ever.
A security breach that reaches customers or surfaces in public has a direct impact on social media reputation and brand trust that can take considerable time to recover. Web security audits are a first line of defence against that scenario.
Taking Web Security Seriously in 2026
Web security audits are not a luxury reserved for large organisations. Any business with a website that collects data, processes transactions, or serves customers online has a responsibility to keep that site secure. If you want to communicate the importance of digital security across your team, video production and training content can build awareness in a format that staff genuinely engage with.
Run web security audits regularly. Keep software updated. Manage access controls carefully. Understand your compliance obligations. Work with digital partners who treat security as a first-class concern.
ProfileTree works with businesses across Northern Ireland, Ireland, and the UK on web design, digital strategy, SEO, and content. Security is part of how we build and maintain digital assets for our clients. If you would like to discuss how web security audits fit into your digital operations, our team is happy to help.
FAQs
How long does a web security audit take?
A standard automated scan with manual review of a small-to-medium business website typically takes four to eight hours. A full penetration test for a larger platform may take several days. Scope it before work begins so timelines are clear.
Do I need external specialists to run web security audits?
For basic configuration reviews, a competent developer or digital agency can handle web security audits. For penetration testing in regulated industries, external specialists with formal certifications are the better choice. They bring independent perspective and fewer blind spots.
What free tools are available for web security audits?
OWASP ZAP, SSL Labs, and Security Headers are all free tools that support web security audits. They are useful for initial checks and ongoing monitoring but provide a baseline rather than a full audit. Use them as part of a broader programme.
What should I do immediately after a web security audit?
Address critical and high-severity findings within 24 to 48 hours. Schedule medium and low issues into your next development sprint. Assign ownership for each item and set a follow-up date to confirm fixes are in place.
How do web security audits relate to SEO?
Google penalises hacked sites and treats HTTPS as a ranking signal. Our SEO services in Belfast always include a technical health check covering HTTPS, security headers, and crawlability, because a secure site is a more rankable site.
Can AI chatbots on my website create security risks?
Yes. AI chatbots introduce attack surface if not properly configured. Web security audits should include a review of chatbot integrations, how they handle user inputs, where conversation data is stored, and whether the platform receives regular updates.