Web Design That Turns Visitors Into Customers
A website that looks good but generates no enquiries is a liability, not an asset. As a website design agency founded in Belfast in 2011, ProfileTree has completed more than 1,000 web projects for businesses across Northern Ireland, Ireland, and the UK. In that time, one truth has stayed constant: the brief you bring us matters as much as the brief we write for you.
Every project we take on starts with a commercial question, not a visual one. What do you want this site to do? Who are you trying to reach? What does success look like in 12 months? The answers shape everything: the structure, the content strategy, the conversion paths, and the technical build.
If you are looking for a website design agency in Belfast that treats your website as a business tool rather than a design exercise, you are in the right place.
What Website Design Means At ProfileTree
Web design is often described as making things look attractive. That is part of it, but only part. A professionally designed website brings together UX (user experience), visual identity, information architecture, mobile performance, page speed, SEO, and conversion strategy into a single, coherent product.
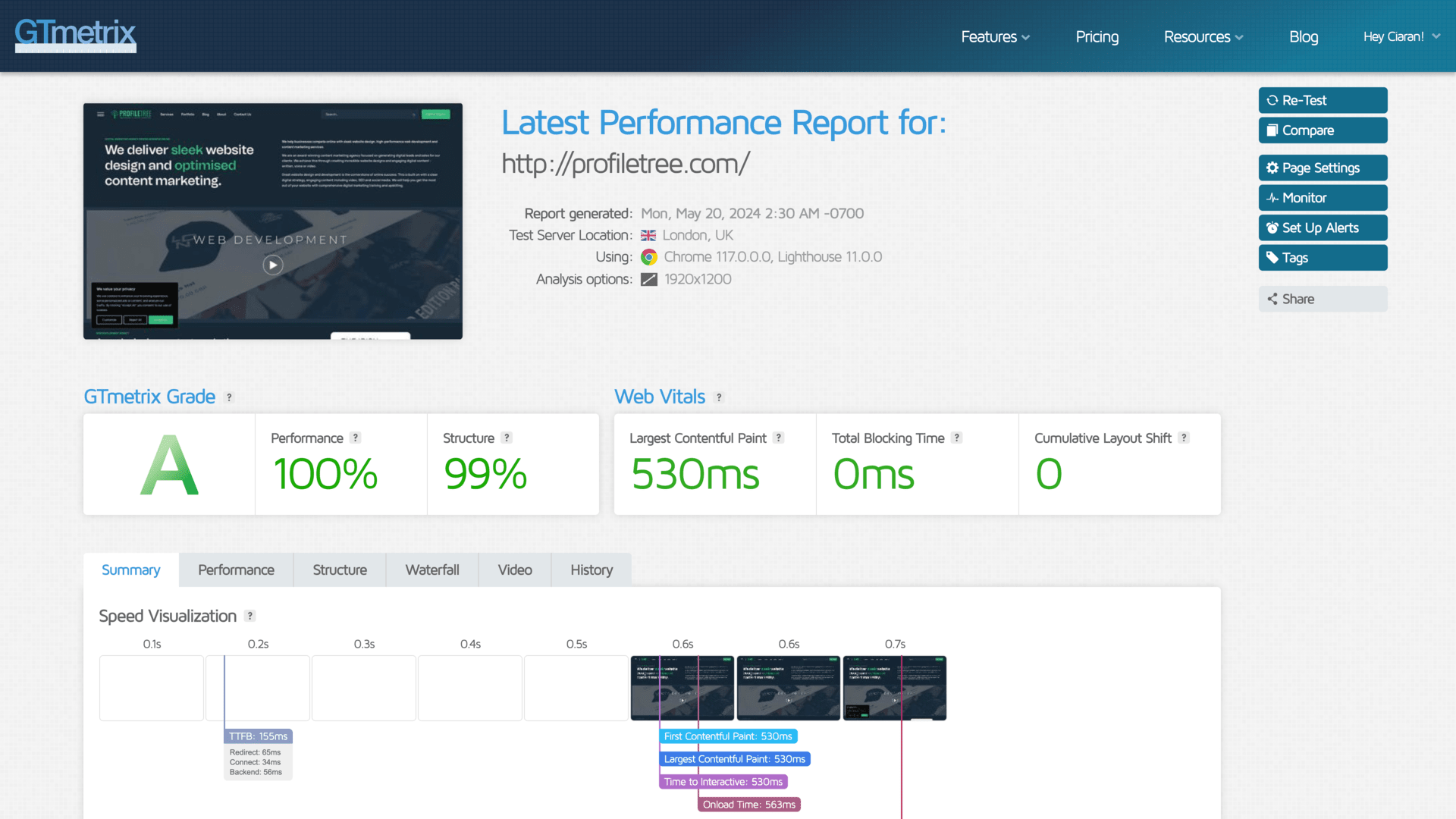
At ProfileTree, our web design process is built on four principles: clarity, speed, discoverability, and conversion. Every visual decision (layout, typography, colour, imagery) is made with those four principles in mind. A button placed in the wrong position costs you enquiries. A page that loads in four seconds instead of two costs you rankings. These are not hypothetical losses; they are measurable ones.
Strategy First
Before a single page is designed, we define what the site needs to achieve. Who is the audience? What do you want them to do when they arrive? Which pages need to rank in search, and for what? A website without a strategy behind it is a brochure. A website with one is a sales tool.
We map out the full site structure, the content requirements, and the conversion paths before any visual work begins. This is where most agencies cut corners, and where most underperforming websites go wrong.
UX and Visual Design
User experience determines how people move through your site. Visual design determines whether they trust it. The two work together: a site that looks polished but confuses visitors will not convert, and a site that is easy to navigate but looks dated will lose credibility before the user reads a word.
Our web designers work from wireframes outward, establishing layout and information hierarchy before applying colour, typography, and imagery. The result is a site that feels considered rather than assembled.
WordPress as Our Core Platform
The majority of our builds use WordPress, which powers around 43% of the web and gives clients full content control without ongoing developer dependency. It is the platform most SEO tools are built around, and it allows your team to update pages, publish content, and manage the site independently once it is live.
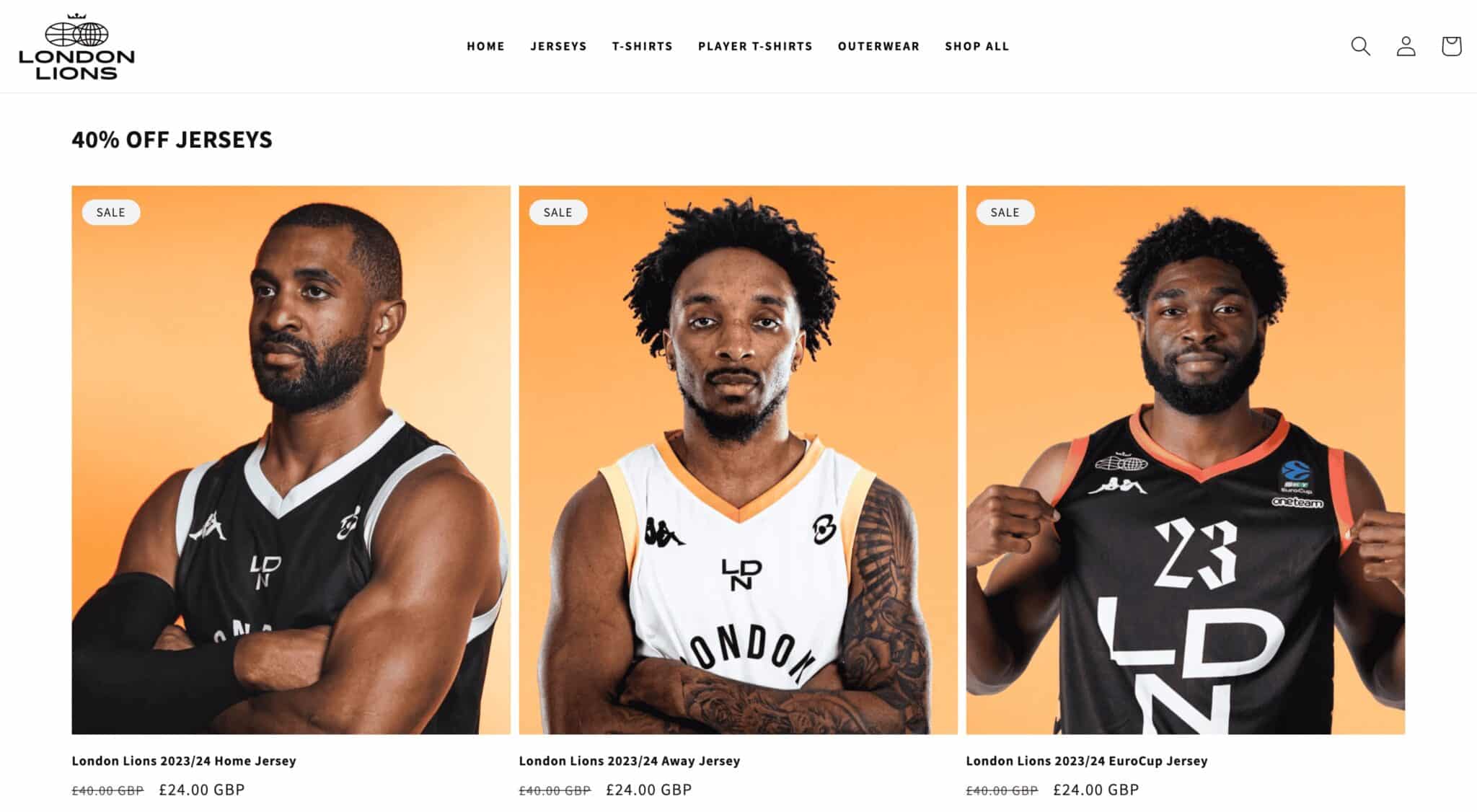
For e-commerce clients, we build on WooCommerce and Shopify, depending on the scale and structure of the product catalogue. For clients with specific technical requirements, we design and build custom solutions where an off-the-shelf platform would create limitations.
Mobile-First, Always
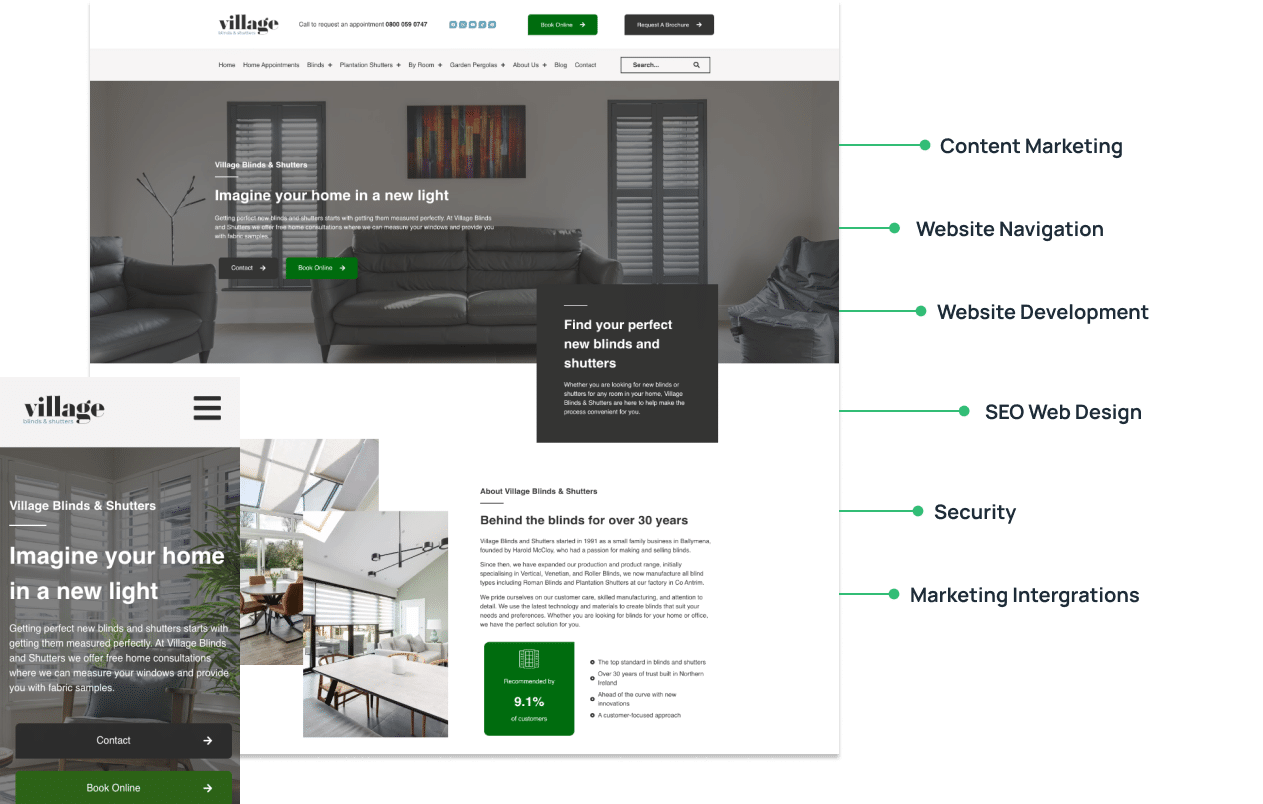
Every build starts from the mobile viewport and scales up, because Google indexes the mobile version of your site first. That has been the case since 2019, and it is not changing. So, we design for mobile viewports before desktop: layout, navigation, button sizing, and image loading are all considered at a small screen scale and then scaled upwards.
A site that looks beautiful on a widescreen monitor but breaks on a smartphone is not a finished project; it is a problem waiting to cost you traffic.
Built to Convert
Conversion is treated as a web design requirement from the start, not something added at the end. CTAs, trust signals, and contact paths are all planned at the wireframe stage. Our builds are also optimised for performance: compressed images, minimal render-blocking scripts, and Core Web Vitals compliance are standard, not optional extras.
“When a website design project goes wrong, it usually fails at the brief stage, not the build stage,” says Ciaran Connolly, founder of ProfileTree. “We spend more time on discovery and planning than most agencies because the decisions made there determine everything that follows.”
You can read more about how we approach the technical side of a build on our website development services page.
Who We Build Websites For
As a website design agency, ProfileTree works primarily with SME owners, marketing managers, and commercial decision-makers across Northern Ireland, Ireland, and the wider UK. Our clients span professional services, manufacturing, hospitality, retail, education, health, and the public sector.
The common thread is not industry; it is intent. Our clients want a website that performs. They have either outgrown their existing site, launched a business and need a professional presence, or seen their traffic or enquiry volume fall and want to understand why. In most of those cases, the answer comes back to the same things: weak technical foundations, poor content structure, or a web design that was built for aesthetics rather than for the user.
We work with businesses at different stages. Some come to us with a clear brief and a deadline. Others need us to define the brief with them. Both are fine. The discovery phase is there precisely for that.
Ready to Grow Online? Start Your Project Today!
- Onpage SEO
- Performance optimisation
- Driving conversions
- Website auditing
- Full branding services
- Website navigation
- Visual displays
- Web design training
Our Web Design Process: Brief to Launch
Understanding what working with a website design agency actually looks like can make the difference between a smooth project and a frustrating one. Here is how we approach a web design project from the first conversation to the day your site goes live.
Discovery and Strategy
Before any web design work begins, we run a discovery session to understand your business, your audience, your competitors, and your goals. We look at your existing website analytics where available, review your current search rankings, and map out the pages and content the new site needs to include.
This stage often surfaces problems the client had not flagged: slow page speeds, cannibalisation between similar pages, or a navigation structure that buries the most important conversion pages.
UX and Wireframing
Once the strategy is agreed, we build wireframes: structural blueprints showing layout and information hierarchy without visual styling. This is where we decide where CTAs sit, how navigation flows, which content appears above the fold, and how a user moves from landing page to conversion point. Getting this right before web design begins saves significant time in revisions later.
Visual Design
With the wireframes signed off, we apply your brand: colours, typography, imagery direction, and visual language. For businesses without a developed brand identity, we can create one. For those with existing brand guidelines, we work within them, or where the brief allows, evolve them. Web design concepts are presented for review and refined before the build begins.
Development and SEO Integration
Our web development team builds to the approved web designs, integrating technical SEO from the ground up: page speed optimisation, clean URL structures, metadata, schema markup, internal linking architecture, and Core Web Vitals compliance. SEO is not bolted on at the end of a ProfileTree project; it is built into the structure from the start.
Testing, Launch, and Handover
Before any site goes live, we test across devices and browsers, check all forms and integrations, run performance audits, and review accessibility compliance. Once the site is live, we provide training on content management so your team can update pages, publish blog posts, and manage the site independently if that is what you want.
The Types of Web Design We Deliver
Every business that comes to ProfileTree has a different starting point, a different audience, and a different definition of what success looks like online. The tab sections below cover the types of web design projects we take on most frequently. If your project sits across more than one category, that is common; most do.
- SEO & Technical
- Custom & WordPress
- eCommerce
- Professional & B2B
- B2C
- Local & Small Business
- Education
- Event
- Hospitality
- Portfolio
- Minimalist
Some agencies treat SEO and technical performance as optional extras. We treat them as preconditions. A site that ranks poorly or loads slowly has failed before a visitor has read a word.
Our SEO and technical builds go beyond metadata and page speed. We map crawl paths, implement structured data, audit Core Web Vitals before launch, and build URL architectures that distribute authority rather than dilute it. For businesses in regulated sectors, we also build to WCAG 2.1 accessibility standards, which is increasingly a requirement for public-sector and enterprise procurement rather than a nice-to-have.
The measure of good technical work is that you never have to think about it.
WordPress is the right choice for most businesses: flexible, well-supported, and genuinely manageable by a non-technical team once the site is live. We build on it from scratch rather than customising off-the-shelf themes, which means the codebase is clean, and the performance profile is predictable.
Where WordPress is not the right fit, we build custom. That applies when the functionality required sits outside what any standard platform handles well: complex user logic, proprietary data integrations, or product configurations that would require so many plugin workarounds.
Custom projects cost more upfront; they are worth it when the fit genuinely matters.

The design decisions that move eCommerce conversion rates are rarely the obvious ones. It is not the hero image or the colour palette. It is the number of steps in the checkout, the behaviour of the mobile cart, how out-of-stock products are handled, and where the primary CTA sits on a product page.
We build on WooCommerce for businesses that need deep WordPress integration and catalogue flexibility, and on Shopify for those who want a managed platform with lower ongoing technical overhead. Both receive the same eCommerce-specific SEO treatment: canonical tags for product variants, structured data for rich results, and category architecture built to avoid self-cannibalisation.
Business buyers visit a site multiple times before making contact. Each visit is an evaluation: does this firm understand our sector, can they deliver at our scale, and do they communicate clearly? A B2B site that cannot answer those questions in the first thirty seconds of browsing loses the lead before it ever arrives.
We design professional and B2B sites around that evaluation process. Content is structured to inform rather than impress. Case studies and credentials are presented where they carry most weight. Contact paths are short and direct. For service businesses where video explains the offer more efficiently than text, our in-house video team can produce content as part of the same project rather than as a separate commission.
Consumer decisions are faster, more emotionally driven, and far less forgiving of friction than B2B ones. A B2C site has seconds to establish trust and a clear path to conversion before a visitor moves on.
We have built B2C sites across travel and tourism, retail, health, charity, agrifood, manufacturing, heritage, and more. The visual approach varies considerably across those sectors. What does not vary is the underlying method: design decisions based on how the target audience actually behaves, not on how the business prefers to present itself.
Brand consistency across digital and physical touchpoints matters more on B2C sites than most clients anticipate, and we factor that in from the wireframe stage.

Local and small business briefs share a common constraint: the site needs to perform without a dedicated person to run it. That shapes every decision, from platform choice to the complexity of the content management workflow.
We design local business websites to rank in service-area searches and convert that traffic quickly. For Belfast and Northern Ireland clients specifically, we understand the cross-border search behaviour between Northern Ireland and the Republic, and the industries where local digital presence makes the most commercial difference.
Clients are trained to manage the site independently so it stays current long after the project closes.
Education sites serve several distinct audiences simultaneously: prospective students, current students, parents, employers, and funding bodies. Each group arrives with different questions and different tolerances for navigational complexity.
At Profiletree, we structure education sites around clear audience pathways rather than institutional hierarchies. We organise course and programme content for scannability and search visibility, not departmental preference. We also reduce enrolment and enquiry processes to the minimum steps required. Check our in-house brand: Learning Mole.
For training providers and further education colleges competing in a search environment where prospective students have high intent and low patience, the difference between a well-structured site and a poorly structured one is measurable in application volumes.
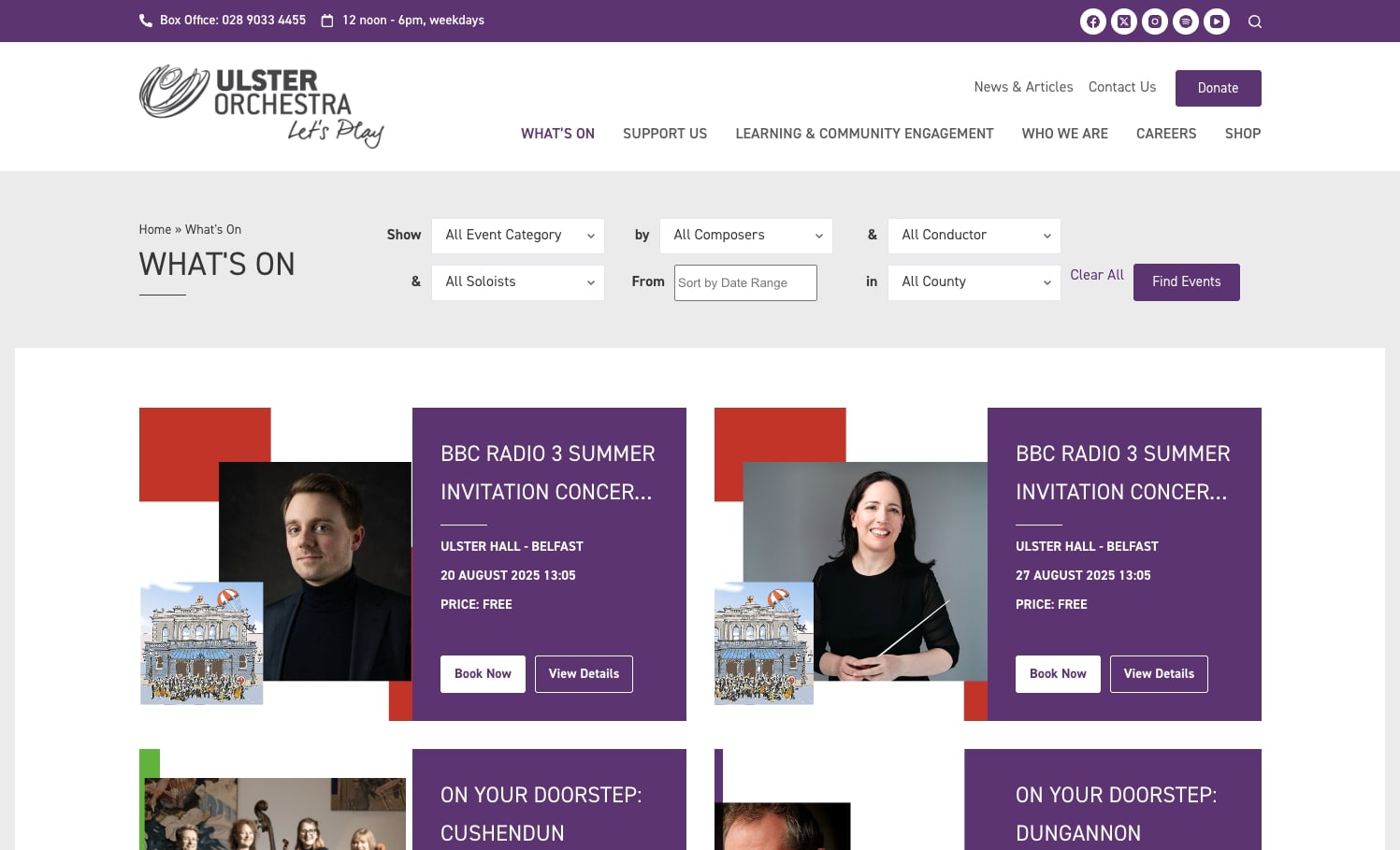
The commercial stakes of an event site are unusually clear: every registration or ticket sale is a direct, traceable outcome. Poor UX, slow load times, or a confusing booking flow have immediate costs that most other site types can absorb more gradually.
We design event sites with one conversion goal at the centre and everything else arranged around it. For recurring events, we build templates that can be updated for subsequent editions without a full rebuild, and URL structures that preserve any search authority accumulated from previous years.
Social sharing and real-time update integrations are planned at the build stage rather than added as afterthoughts.
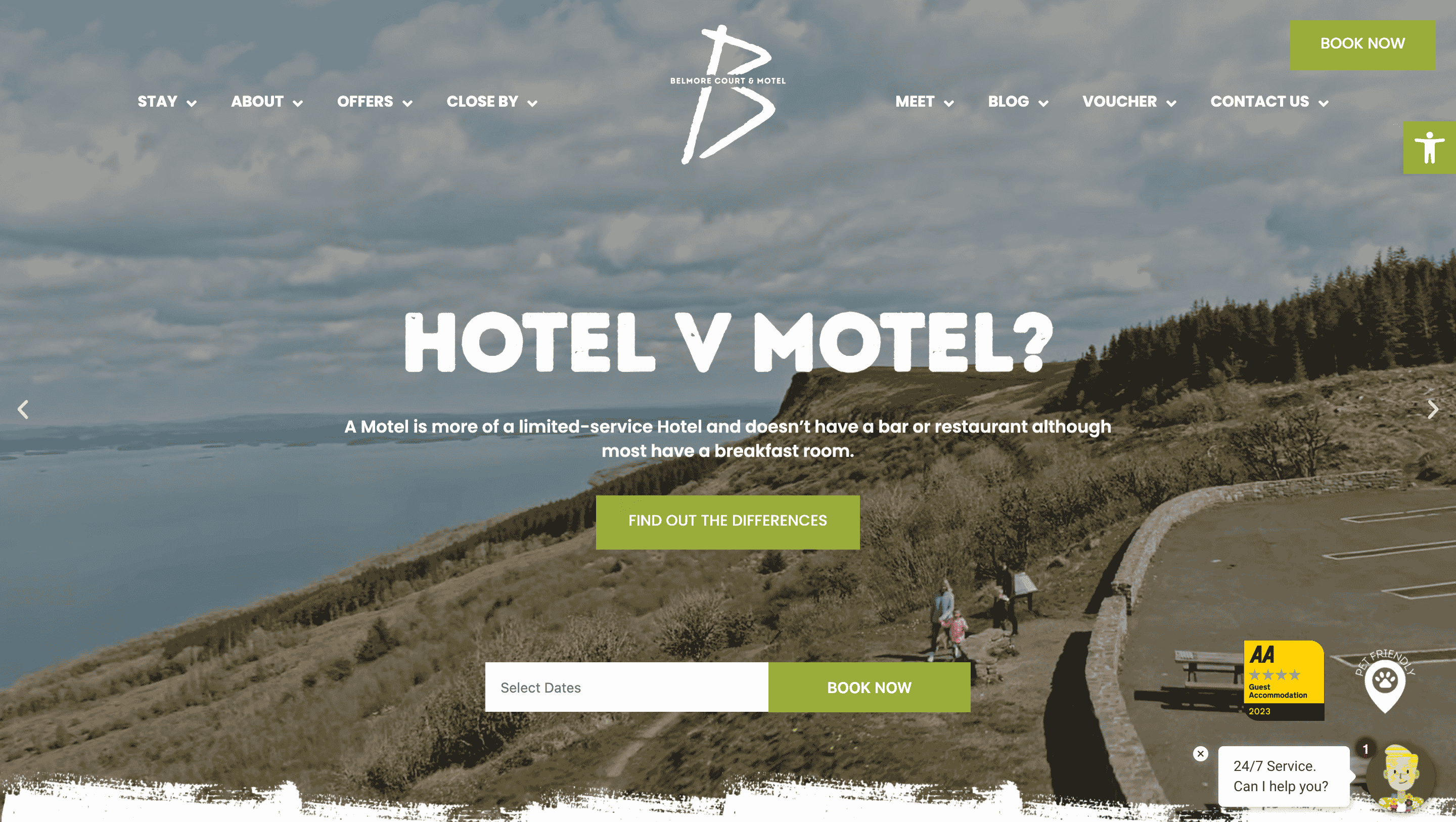
A hospitality site is selling an experience before the guest has had it. The visual quality of the site and the ease of the booking process are both part of that pre-arrival impression, and both need to work.
High-resolution imagery and video are often essential for hospitality clients, but they can incur performance costs if not handled correctly. We manage that trade-off at the build stage: image compression, lazy loading, and CDN delivery keep pages fast without sacrificing visual quality. We also build in booking system integration, availability tools, and review display from the start, rather than bolt them on later.
A portfolio site needs to do two things: show the work at its best, and move an interested visitor toward making contact. Most portfolio sites do the first reasonably well and the second very poorly.
We design portfolio sites around the viewer’s journey rather than the creator’s filing system. The strongest work leads. We include filters by project type or sector, where the body of work is large enough to warrant them. Contact options are present at every stage of browsing, not only at the end. For image-heavy portfolios, load performance is treated as a design requirement: high-resolution work displayed on a slow site undermines the quality signal it is supposed to create.

Minimalist design is a discipline, not a style preference. Removing elements that do not carry weight requires more considered decision-making than adding them, and the result needs to work harder because there is less to fall back on.
We apply minimalist principles where the brief genuinely calls for them: premium brands where the product or work needs to be the dominant visual, single-service businesses where simplicity accelerates the decision, and clients where a cluttered site would contradict the brand positioning.
The commercial logic is sound: fewer distractions produce clearer conversion paths, and leaner pages load faster. Both outcomes are measurable.
What Affects the Cost of a Website Design Project
One of the most common questions we receive (and one of the least honestly answered across the industry) is how much a website costs. The truthful answer is that it depends, but we can be specific about what it depends on.
Scope and Page Count
A six-page brochure site for a local service business sits in a very different bracket to a 50-page e-commerce build with custom product filters and a third-party fulfilment integration. More pages, more complexity, more time.
Custom Design vs Template-based
A fully bespoke visual design costs more than a well-customised premium theme. For many SMEs, a theme-based build with strong customisation delivers 90% of the visual quality at a fraction of the cost.
Functionality Requirements
Booking systems, membership portals, calculators, live chat integrations, multilingual support, CRM connections: each adds to the build time and therefore the cost.
Content
If you provide all copy, images, and assets, the project scope is smaller. If you need us to write the content, commission photography, or develop a content strategy alongside the site, that is additional work.
For most SME clients in Northern Ireland and Ireland, a professional WordPress website design project sits broadly in the £3,000 to £15,000 range. Enterprise-level or custom-build projects can go higher. We are transparent about this early in every conversation because we would rather lose a project at the proposal stage than take on a brief we cannot deliver within a client’s realistic budget.
How Long Does a Web Design Project Take?
Timelines depend on scope, but the honest answer is that most projects run longer than clients expect — and the delay usually comes from the client side, not ours. Feedback rounds, content sign-off, and stakeholder approvals are where time is lost on most projects. Knowing that going in makes it easier to plan around.
Here is a realistic breakdown by project type:
The single biggest factor in whether a project lands on time is how quickly the client can review and respond at each stage. We build agreed turnaround windows into every project timeline from the start, so both sides know what is expected and when.
6 to 8 weeks from signed brief to launch. Assumes client provides all content and feedback is returned within agreed windows.
8 to 12 weeks. Discovery and wireframing take two to three weeks; design and development take four to six; testing, revisions, and launch take the remainder.
12 to 16 weeks for a standard catalogue. Larger builds with custom functionality, third-party integrations, or complex product structures run to 18 to 24 weeks.
Scoped individually. Discovery alone typically takes two to four weeks before any design work begins.
Not sure what your project scope looks like yet? We offer a free initial consultation!
How Web Design Connects to SEO and Conversion
Design and SEO are not separate disciplines. The choices made during a web design project have a direct impact on how well a site ranks and how many of its visitors convert into customers.
Page Speed
Page speed is a confirmed Google ranking factor. A site that takes more than three seconds to load on mobile loses a significant proportion of its visitors before they have seen a single word of content. Our builds are optimised for performance: compressed images, minimal render-blocking scripts, server-side caching, and CDN delivery.
Content Structure
Content structure (heading hierarchy, semantic HTML, schema markup) makes it easier for search engines to understand what each page is about and match it to the right queries.
Site Architecture
Site architecture determines how Google crawls and indexes your pages, and how link equity flows through the site. A flat, logical structure with clear internal linking helps both search engines and real users find what they are looking for.
Conversion Rate
Conversion rate is ultimately what turns a well-designed, well-ranked site into a business asset. We design with conversion paths in mind: clear CTAs above the fold, trust signals near decision points, forms with minimal friction, and contact options that match how your audience actually wants to get in touch.
What to Look for When Choosing a Website Design Agency
Choosing the right website design agency is one of the more consequential decisions a business makes. A poor choice costs time, money, and often rankings that take months to recover. Before you appoint a website design agency, here is what to look at.
A good-looking screenshot tells you very little. Ask whether the sites in their portfolio still rank, whether they load quickly, and whether the businesses they were built for saw measurable results.
Can the agency explain their web design process step by step? Do they have a discovery phase? How do they handle revisions? Vague answers here usually mean vague project management.
If an agency builds websites without building SEO in from the start, you will pay twice: once for the site and once for someone to fix the technical problems it creates. Ask specifically how metadata, site speed, and schema are handled in the web design process.
Who will you be dealing with? How often will you receive updates? What is the escalation path if something goes wrong? At ProfileTree, you work with a named project lead throughout.
What happens when the site goes live? Is there a support period? Who do you contact if something breaks? A website is not a finished product on launch day; it needs ongoing attention.
What Our Clients Say
ProfileTree holds a 5-star rating on Google, based on more than 460 verified reviews. These three reviews reflect what clients working with our website design agency most consistently tell us.
"Excellent experience with Profile tree Web Design. Gabbi was especially helpful; she guided me through the web design process clearly and also helped me understand and use AI tools effectively. Professional, supportive, and highly recommended."
John Callaghan
"My business used the amazing services of profile tree to create a professional website that now replaces a lot of the work we had to do previously to manually engage and update our customers. Khadiza used our sessions so efficiently to literally built the website we desired on each call and helped us to collaborate on what is best for our clientele from her professional experience. We are so grateful for her hard work and patience."
Ermis Dacaj
"Brilliant service. ProfileTree built a lovely new website for us, and it was stress-free as these things go! Highly recommend."
Tina
ProfileTree: Your Website Design Agency in Belfast
If you are ready to start a web design project or want an honest assessment of what your current site needs, we would like to hear from you. ProfileTree has been building websites for businesses across Belfast, Northern Ireland, Ireland, and the UK since 2011. Over 1,000 projects completed. 5-star rated on Google.
FAQ’s
For most SME clients in Northern Ireland, Ireland, and the UK, a professionally designed WordPress site sits in the £3,000 to £15,000 range. The variables are scope (page count and complexity), the level of custom design, functionality requirements, and whether content production is included. We provide fixed-price proposals once we understand your brief.
A straightforward brochure site typically takes six to ten weeks from signed brief to launch. An e-commerce build or a site requiring custom functionality usually runs twelve to eighteen weeks. Timelines depend partly on us and partly on how quickly client feedback and sign-offs come back, so responsiveness during the project matters on both sides.
At ProfileTree, a web design project typically includes: discovery and strategy, UX wireframing, visual design, WordPress or platform development, technical SEO setup, mobile and browser testing, performance optimisation, content management system training, and post-launch support. Copywriting, photography, and ongoing SEO can be included or scoped separately.
Not every business needs a full rebuild. If your site has strong content, a reasonable structure, and no serious technical problems, a redesign or targeted optimisation work may deliver better results at lower cost. We carry out website audits that give you a clear view of what is working, what is not, and what the most cost-effective path forward looks like.
Web design covers the strategic, visual, and UX decisions: what the site looks like, how it is structured, how users move through it, and how it reflects your brand. Web development is the technical build that brings those designs to life: the code, the platform configuration, the integrations, and the performance engineering.
At ProfileTree, both disciplines sit within the same team, which means web design decisions are made with technical constraints in mind from the start.
Yes. We work with businesses across Ireland, the UK, and internationally. The majority of our projects are delivered remotely, so location is rarely a practical barrier. We have completed projects for clients across England, Scotland, Wales, and the Republic of Ireland alongside our Northern Ireland work.
Every site we build includes technical SEO as standard: clean URL structure, metadata, schema markup, page speed optimisation, and correct heading hierarchy. That gives the site a solid foundation. Ranking for competitive terms takes ongoing content and SEO work beyond the build itself, which we can scope separately if needed.
Yes. A full rebuild is not always the right answer. We assess what is working, what is not, and recommend the most cost-effective route, whether that is a full redesign, a targeted refresh, or technical fixes to the existing site.
We provide a handover session covering content management, so your team can update the site independently. Beyond that, we offer ongoing support, hosting, and SEO retainers for clients who want continued involvement. There is no obligation to continue after launch.
Web Design
We design stunning, user focused websites that present your brand beautifully and convert visitors into customers.
Web Development
We use the latest development tools to build websites that are optimised for peak performance at all times.
Website Hosting
We manage everything from site updates and reports to hosting, allowing you to focus on running your business.
Search Engine Optimisation
Using the latest SEO techniques, we help your brand get found for the right terms and by the right people.
Digital Marketing Strategy
Navigate the digital landscape with a marketing strategy. Our team crafts comprehensive plans that resonate with your target audience, drive engagement, and boost conversions.
Digital Marketing Training
Elevate your digital proficiency. Our in-depth training sessions equip your business with cutting-edge digital marketing techniques to outperform competitors and thrive online.
Social Media Strategy
Captivate and grow your social following. We create tailored social media strategies that ignite engagement, amplify your brand's online presence, and foster lasting connections.
Email Marketing Solutions
Harness the power of your mailing list. Our precision-targeted email marketing campaigns are engineered to nurture relationships and drive tangible business outcomes.
Content Marketing Services
Elevate your brand with our content marketing mastery. From thought-provoking blogs to eye-catching infographics, we craft content that captivates, informs, and converts your ideal audience.
Video Production
Capture your audience with compelling video content. Our production team creates visual stories that engage, inform, and leave a lasting impression.
Brand Storytelling
Bring your brand's story to life with authenticity. We craft compelling narratives that strike a chord with your audience, forging a powerful emotional bond with your brand.
Content Strategy Development
Strategic content that drives action. We develop content strategies that align with your business goals, ensuring every piece of content counts.
AI Training
Empower your business with AI expertise. Our tailored training demystifies AI, equipping your team with the knowledge to leverage its potential for growth and innovation.
AI Chatbots
Transform customer service with AI chatbots. We develop sophisticated chatbots that elevate user experience, streamline interactions, and deliver unparalleled efficiency.
AI Marketing
Transform your reach with AI-driven marketing. Harness data-driven insights for laser-targeted campaigns that captivate, engage, and convert your audience.
AI Tools for Business
Optimise your operations with cutting-edge AI tools. We integrate intelligent solutions that streamline processes, enhance efficiency, and support data-driven decision-making.
Join Our Mailing List
Grow your business with expert web design, AI strategies and digital marketing tips straight to your inbox. Subscribe to our newsletter.