Secure Login Practices for Web Applications
Table of Contents
In the time it takes you to read this paragraph, automated bots will have attempted to breach thousands of accounts globally. For businesses running web applications, secure login practices are no longer a technical checkbox. They are a direct line of defence against financial loss, reputational damage, and regulatory penalties. At ProfileTree, Belfast’s digital agency specialising in web design, development, SEO, and digital transformation, we see the consequences of poor authentication first-hand when clients come to us after incidents. Secure login practices must be built into every project from day one, not retrofitted when something goes wrong.
This guide covers the full picture: from the fundamentals of passwords and multi-factor authentication through to SSL implementation, session management, access controls, and the growing shift towards passkeys. Whether you manage a small business website or a complex web application serving thousands of users, these secure login practices apply. We have written this for both technical developers and business owners who need to understand what their teams should be implementing.
Authentication Methods: The Modern Hierarchy

Not all login methods offer the same level of protection. Understanding the range of options and where each sits on the security spectrum is the starting point for any serious review of secure login practices. The landscape has shifted considerably over the past two years, and businesses still relying solely on passwords are operating with a significant gap in their defences.
Why Passwords Alone Are No Longer Sufficient
A password is a single point of failure. If a user reuses the same password across multiple services and one of those services suffers a breach, every account using that password becomes vulnerable through credential stuffing. Businesses that plan their authentication model early, ideally during the build phase with a specialist in website development for SMEs, are in a far stronger position than those who retrofit security later. Secure login practices begin with enforcing strong, unique passwords, but they cannot end there.
Passwords should be enforced with a minimum length of 12 characters combining uppercase letters, lowercase letters, numbers, and symbols. Password reuse across services should be actively discouraged, and integration with a reputable password manager should be encouraged in your onboarding documentation. Secure login practices at the password level also mean hashing credentials using bcrypt, PBKDF2, or Argon2 before storage. Never store passwords in plain text, and always apply a salt to prevent rainbow table attacks.
Multi-Factor Authentication
Multi-factor authentication (MFA) adds a second verification layer that makes it considerably harder for attackers to access accounts even when a password has been compromised. Secure login practices built around MFA require users to provide something they know (a password), something they have (a mobile device or hardware token), or something they are (a biometric such as a fingerprint or facial recognition).
Not all MFA methods are equal. SMS-based codes carry a known vulnerability: SIM swapping attacks, where a criminal convinces a mobile carrier to redirect a user’s number to a new device, can intercept SMS codes entirely. Keeping your server environment patched and correctly configured is equally important to your overall security posture. ProfileTree’s website security management service covers the infrastructure layer that supports your secure login practices, including updates, monitoring, and configuration hardening. For the authentication layer itself, authenticator applications such as Microsoft Authenticator or Authy are more reliable than SMS, generating time-based codes locally on the device rather than transmitting them over a network. Hardware security keys such as YubiKey represent the strongest available option for high-value accounts.
Passkeys: The Future of Secure Login Practices
The most significant shift in secure login practices in recent years is the move toward passkeys, based on the FIDO2 and WebAuthn standards. A passkey replaces the traditional password with a cryptographic key pair. One part is stored on the user’s device; the other is held by the website. Authentication uses the device’s biometric (Face ID or a fingerprint), and no secret is transmitted across the network.
Passkeys are phishing-proof by design. There is no code for an attacker to intercept or trick a user into revealing on a fake website. If a server is breached, the attacker gains nothing because the user’s private key never left their device. Deciding whether to implement passkeys now or plan for them in the next release is a digital strategy decision for your business, not purely a technical one. For businesses reviewing secure login practices in 2025 and beyond, passkeys should be a priority for any application handling sensitive user data.
| Method | Security Level | Phishing Resistant | Recommended For |
|---|---|---|---|
| Password only | Low | No | No use case |
| Password + SMS code | Medium | Partial | Low-risk accounts only |
| Password + Authenticator App | High | Yes | Email, CRM, banking |
| Hardware Security Key | Very High | Yes | Admin accounts, finance |
| Passkey (Biometric) | Highest | Yes | All critical accounts |
SSL, TLS and Secure Communication Protocols
Secure login practices do not exist in isolation. The channel through which credentials are transmitted must also be protected. Without encrypted communication, even a strong password can be captured in transit by an attacker monitoring the network. This section covers the protocols that underpin secure communication between a browser and a web server.
SSL and TLS Implementation
Secure Sockets Layer (SSL) and its successor, Transport Layer Security (TLS), create an encrypted connection between the user’s browser and your web server. When correctly implemented, this prevents anyone monitoring the network from reading the data in transit. The padlock icon visible in a browser’s address bar indicates an active HTTPS connection, signalling that the site uses TLS encryption.
Secure login practices demand that you use the latest version of TLS. TLS 1.3 offers both improved security and better performance than its predecessors. Older versions such as SSL 3.0 and TLS 1.0 contain known vulnerabilities and should be disabled on your server. Many UK hosting providers enable TLS automatically, but you should verify the configuration and ensure HTTP requests are redirected to HTTPS. Our related guide on protecting user data and secure storage techniques covers how TLS fits into the broader data protection picture for web applications.
Secure Cookies and Session Management
Once a user authenticates, their session is typically maintained through a cookie or session token. Secure login practices extend to how these are handled. Cookies should be set with the Secure attribute, ensuring they are only transmitted over HTTPS. They should also carry the HttpOnly attribute, which prevents JavaScript from accessing the cookie and reduces the risk of XSS attacks stealing session data.
Session tokens should be unique, random, and long enough to make guessing impossible. They should be regenerated after each successful login to prevent session fixation attacks. Expiry policies are also part of secure login practices: sessions should expire after a reasonable period of inactivity, and users should be able to invalidate all active sessions from their account settings. For a broader overview of controls that complement session management, our guide on six ways to make your website secure covers complementary measures worth reviewing alongside this article.
Protecting Sensitive Data
Secure login practices are inseparable from broader data protection obligations. Every piece of data collected during an authentication process, including usernames, email addresses, passwords, and device fingerprints, carries legal and ethical obligations under UK GDPR and the Data Protection Act 2018. This section covers what to protect, how to protect it, and the consequences of getting it wrong.
Encryption at Rest and in Transit
Credentials must be protected both while stored and while being transmitted. Secure login practices for data in transit rely on TLS, as described above. For data at rest, passwords should never be stored in a recoverable format. Use hashing algorithms such as bcrypt, PBKDF2, or Argon2, all of which incorporate a work factor that makes brute-force attacks computationally expensive. Salting each hash individually prevents attackers from using precomputed tables to crack multiple passwords simultaneously.
Sensitive data such as personal identifiers or payment details should be encrypted using AES. Access to decryption keys must be strictly controlled and logged. Only the minimum necessary data should be collected and retained. Under UK GDPR, you are required to implement appropriate technical and organisational measures to protect personal data, and solid secure login practices form part of that obligation. Communicating your security posture clearly to customers builds trust; ProfileTree’s content marketing service can help you translate complex security measures into plain language that users will understand and value.
Handling Account Recovery Securely
Account recovery is often the weakest point in an otherwise strong security setup. Secure login practices must extend to what happens when a user cannot access their account. Security questions based on publicly available or guessable information offer minimal protection. If your application still uses security questions, treat the answers as passwords: require a random string stored in a vault rather than a genuine personal answer.
A more robust approach is to route password reset requests through a verified secondary email address or phone number, both of which must themselves be protected with MFA. The recovery email should have higher security controls than the account it protects, not lower. Time-limiting recovery links to 15 to 30 minutes reduces the risk of an old link being exploited.
“Security is not something you bolt on at the end of a project. When we build web applications for clients, we design authentication from the ground up, including how accounts are recovered and how sessions expire. The businesses that get into difficulty are usually the ones who treated secure login practices as someone else’s responsibility.” Ciaran Connolly, Founder, ProfileTree
Access Control, Input Handling and Defensive Coding
Secure login practices in code go well beyond the login form itself. The way your application handles user input, assigns permissions, and validates requests throughout the session determines whether a successfully authenticated user can still be exploited. These are the principles that separate a well-built web application from one that is merely protected at the front door.
The Principle of Least Privilege
Every user, process, and system component should operate with the minimum permissions necessary to carry out its function. This is the principle of least privilege and forms a core part of secure login practices at the application architecture level. An editor does not need access to user data. A customer portal user does not need access to payment configuration. A read-only API key should not carry write permissions.
Implementing role-based access control (RBAC) formalises this approach. Roles are defined with specific permissions, and users are assigned to roles rather than receiving permissions individually. When an employee leaves or changes role, access is updated at the role level rather than requiring manual changes to individual accounts. If you are integrating automated tools such as AI chatbots on your website, it is essential that the chatbot’s API credentials are scoped to the minimum permissions required and rotated regularly, treating them as an extension of your wider secure login practices.
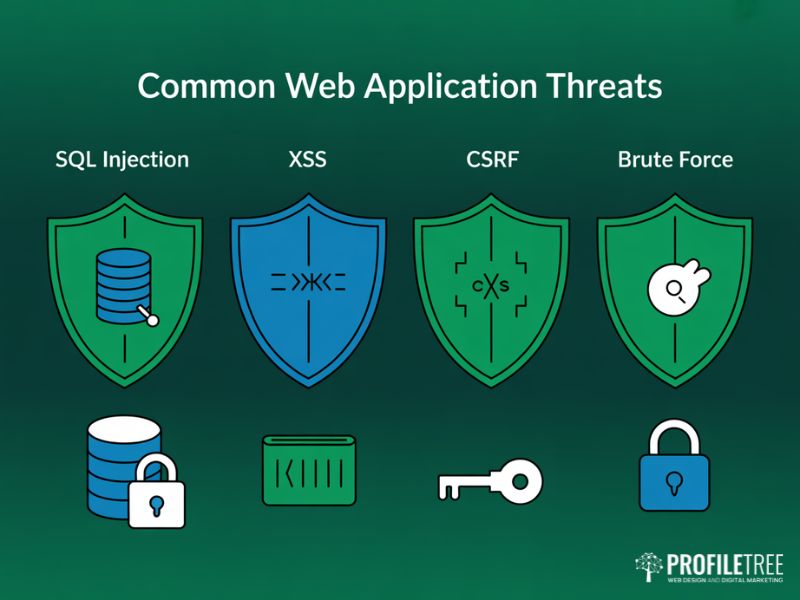
Input Validation and Protection Against Common Attacks
Secure login practices include robust validation of every piece of data submitted by users. SQL injection occurs when an attacker submits malicious code through an input field that is then executed against the database. Parameterised queries and prepared statements prevent this by keeping user input entirely separate from the query structure. It is worth noting that proper HTTPS implementation and clean technical architecture also benefit your search visibility; ProfileTree’s SEO services in Northern Ireland include technical audits that identify security misconfigurations which can simultaneously harm rankings and expose your application to attack.
Cross-site scripting (XSS) attacks inject malicious scripts into pages that are then executed in other users’ browsers. Encoding all output before rendering it in a browser prevents this. Cross-site request forgery (CSRF) tricks authenticated users into submitting requests they did not intend to make. Anti-CSRF tokens, unique values embedded in forms and validated on submission, provide the standard defence. The OWASP Foundation’s Web Application Security Testing Guide is the definitive external reference for any development team implementing these controls and should be bookmarked as part of your secure login practices review.
| Vulnerability | Attack Type | Defence |
|---|---|---|
| SQL Injection | Malicious database queries via input fields | Parameterised queries and prepared statements |
| XSS | Injected scripts run in user browsers | Output encoding before rendering |
| CSRF | Forged requests from authenticated sessions | Anti-CSRF tokens in all forms |
| Session Hijacking | Stolen session cookies used to impersonate users | HttpOnly + Secure cookie attributes, session rotation |
| Brute Force | Automated password guessing | Rate limiting, CAPTCHA, account lockout |
Secure Login Practices for UK Businesses
UK businesses face specific obligations and threat contexts that make secure login practices both a legal requirement and a commercial necessity. This section covers what SMEs and larger organisations need to know about compliance, ongoing security management, and how to apply secure login practices across the entire organisation rather than just the technical team.
UK GDPR, Cyber Essentials and the NCSC
Under UK GDPR and the Data Protection Act 2018, organisations are legally required to implement appropriate technical and organisational measures to protect personal data. Weak authentication, inadequate session management, or poor credential storage are not just security failures; they are potential regulatory breaches that can result in Information Commissioner’s Office (ICO) enforcement action and significant fines.
The National Cyber Security Centre (NCSC) provides practical guidance on secure login practices through its Cyber Essentials scheme. Cyber Essentials certification is mandatory for certain government contracts and widely recognised as a baseline standard across UK industry. You can review the full scheme requirements on the NCSC Cyber Essentials guidance page. For businesses handling customer data through web applications, achieving Cyber Essentials is a credible way to demonstrate that your secure login practices meet a recognised UK standard.
Security Monitoring and Incident Response
Implementing secure login practices is an ongoing process, not a one-time task. Web application firewalls (WAFs) filter incoming traffic and block known malicious patterns in real time. They are configurable to the specific requirements of your application and can be updated as new threats emerge. Monitoring and logging are equally important: every login attempt, successful or failed, should be recorded with a timestamp, IP address, and device identifier.
When a breach does occur, the quality of your incident response plan determines how quickly you can contain the damage. This means knowing which accounts have been affected, being able to force re-authentication across active sessions, and having a process for notifying affected users and the ICO within the 72-hour window required by UK GDPR. Secure login practices embedded throughout the architecture make incident response considerably more manageable because the audit trail is already in place.
Applying Secure Login Practices Across Your Organisation
Technology controls are only part of the answer. Secure login practices depend equally on the people using them. Staff training should cover phishing recognition, the risks of password reuse, and the correct use of MFA. Policies should set clear expectations: default passwords must be changed, shared accounts are prohibited, and access requests require approval. ProfileTree’s digital training for business teams covers cyber awareness as part of a broader programme to help staff across Northern Ireland and the UK work confidently and securely online. For SMEs, a one-page written authentication policy reviewed annually represents a significant improvement over no policy at all.
ProfileTree works with businesses across Northern Ireland, Ireland, and the UK to build websites and web applications where security is designed in rather than added on. Teams adopting AI marketing and automation tools need to pay particular attention to how those integrations authenticate with third-party APIs; weak API key management is increasingly a vector for breaches. If your current platform was built without a structured approach to secure login practices, an audit is the right starting point.
Next Steps for Your Web Application
Secure login practices are a continuous discipline, not a project with a defined end date. The threat landscape changes, standards evolve, and the applications you build today may serve users for years into the future. Start by auditing your current authentication setup against the framework in this guide. Enable MFA, review your session management configuration, check your TLS version, and confirm that credentials are hashed correctly. If you are building a new application, passkeys should be on your roadmap from the start.
ProfileTree, Belfast’s web design and digital development agency, builds web applications with security built into the architecture from the first sprint. A data breach does not only carry regulatory risk; the reputational damage played out across digital channels can take months to repair, which is why teams responsible for social media marketing and brand reputation should be part of any incident response planning alongside your technical team. If you would like a review of your current secure login practices or want to discuss a new project with authentication requirements, our team works with businesses across Northern Ireland, Ireland, and the UK.
FAQs
What is the most important step in secure login practices?
Enable multi-factor authentication on every account with access to sensitive data or administrative functions. Secure login practices without MFA leave you exposed to credential stuffing attacks, which are now largely automated.
Is HTTPS sufficient on its own for secure login?
No. HTTPS encrypts data in transit, which is necessary, but does not protect against weak passwords, poor session management, or application-level attacks such as XSS and CSRF.
How often should session tokens be rotated?
Tokens should be regenerated immediately after each login. Apply an absolute expiry of 8 to 24 hours and an idle expiry of 15 to 30 minutes for applications handling sensitive data.
What are passkeys and should we implement them?
Passkeys use public key cryptography to replace passwords entirely. They are phishing-proof and backed by the FIDO2 standard supported by Apple, Google, and Microsoft. New applications should implement them from the start.
How do secure login practices relate to UK GDPR compliance?
UK GDPR requires appropriate technical measures to protect personal data. Authentication controls are directly relevant to that requirement, and an ICO audit will examine whether they were proportionate to the risk.
What should be included in a web application security audit?
The audit should cover authentication configuration, session management, input handling, access controls, and infrastructure. It should also review front-end build quality; poor website design patterns such as inline scripts or unverified third-party widgets can introduce XSS vulnerabilities that undermine otherwise solid secure login practices.