Deepfake Detectors: Protecting Digital Trust from AI Misinformation
Table of Contents
Your brand’s reputation can be destroyed in minutes by a single convincing deepfake video. The technology that once required Hollywood studios now runs on smartphones, creating indistinguishable fake content that spreads faster than deepfake detectors can respond. Every business faces an unprecedented threat: competitors, disgruntled employees, or random bad actors can fabricate damaging content about your company that millions will believe before you even know it exists.
This guide examines deepfake detectors fighting back, the trust challenges reshaping digital marketing, and the protective strategies your business needs to implement today.
The Deepfake Threat Landscape for UK Businesses
Deepfakes have evolved from amusing celebrity face-swaps to sophisticated weapons targeting businesses across the UK and Ireland. The statistics paint a sobering picture: deepfake creation increased by 900% year-on-year, with business-targeted attacks growing fastest. Your company doesn’t need to be famous to become a target—small businesses increasingly face deepfake extortion, fake executive communications, and manufactured scandal videos designed to destroy local reputations.
The accessibility of deepfake technology fundamentally changed the threat equation. Free apps create convincing face-swap videos in seconds. Open-source voice cloning requires just three seconds of audio to replicate someone’s speech patterns. Text-based AI generates fabricated quotes and statements indistinguishable from genuine communications. The tools that enable creation far outpace those designed for detection, creating an asymmetric battlefield where attackers hold significant advantages.
Northern Ireland businesses face unique vulnerabilities. Smaller markets mean reputational damage spreads quickly through tight-knit business communities. A deepfake video of a Belfast restaurant owner making offensive comments could circulate through local WhatsApp groups and Facebook communities before any response becomes possible. The intimacy of local markets that typically benefits small businesses becomes a liability when false content goes viral.
Financial implications extend beyond immediate reputational damage. Share prices drop an average of 3% following deepfake incidents involving public companies. Small businesses report customer losses between 15-30% after deepfake attacks, with recovery taking months or years. Legal costs for pursuing perpetrators often exceed £50,000, assuming you can even identify them. Insurance companies increasingly exclude deepfake-related losses from standard business coverage, leaving companies exposed to potentially devastating financial impacts.
The sophistication gap between creation and detection continues widening. While detection tools improve, deepfake technology advances faster. Today’s undetectable deepfakes become tomorrow’s obvious fakes, but by then, more sophisticated versions emerge. This technological arms race means businesses must prepare for a future where distinguishing real from fake becomes increasingly difficult, potentially impossible.
Understanding Deepfake Technology: Know Your Enemy
Understanding how deepfake creation works provides crucial context for selecting appropriate deepfake detectors and defensive strategies. This technical knowledge helps businesses assess vulnerabilities and implement targeted protection measures.
Visual Deepfakes: Beyond Simple Face Swaps
Modern visual deepfakes transcend basic face replacement, incorporating subtle details that fool even careful observers. Advanced algorithms replicate micro-expressions, breathing patterns, and involuntary movements that our brains use to assess authenticity. The technology analyses thousands of hours of target footage, learning unique mannerisms and reproducing them perfectly.
Generative Adversarial Networks (GANs) power most sophisticated deepfakes. Two AI systems compete against each other—one creates fakes, while the other detects them. Through millions of iterations, the creator learns to fool the detector, eventually producing content that defeats most detection methods. This self-improving process means deepfakes get better automatically without human intervention.
Real-time deepfakes represent the next evolution. Rather than pre-recorded videos, live deepfake technology enables real-time impersonation during video calls. Criminals already use this technology for fraud, impersonating executives to authorise fraudulent transfers. The implications for business communications are staggering—every video call becomes potentially suspect.
Body puppeteering extends beyond faces to entire physical performances. AI maps one person’s movements onto another’s body, creating videos of people doing things they never did. A competitor could create footage of your employees mishandling products, violating safety protocols, or engaging in inappropriate behaviour. The technology is convincing enough that viewers rarely question what they’re seeing.
Environmental manipulation adds another layer of deception. AI doesn’t just fake people—it fabricates entire scenes. Your pristine showroom becomes a chaotic mess. Your professional office transforms into an unprofessional environment. These environmental deepfakes prove particularly damaging for businesses relying on physical premises for credibility.
Audio Deepfakes: The Invisible Threat
Voice cloning technology poses perhaps the greatest immediate threat to businesses. Unlike video deepfakes requiring significant processing power, audio deepfakes run on standard computers in real-time. Three seconds of recorded speech—from a voicemail, video, or phone call—provides enough data to clone someone’s voice convincingly.
The technology captures not just tone and accent but speaking patterns, vocabulary choices, and emotional inflexions. AI learns how individuals structure sentences, their preferred phrases, and speech rhythms. The result sounds more authentic than human impersonators because it’s based on actual speech patterns rather than interpretation.
Phone-based attacks using voice cloning already cost businesses millions. Criminals clone executive voices to authorise wire transfers, change supplier details, or request sensitive information. The BBC reported that a UK energy firm lost £200,000 to voice-cloning fraud, with the CEO’s “voice” instructing urgent transfers. These attacks succeed because they exploit trust in familiar voices.
Podcast and video content provide attack vectors for voice cloning. Every speaking engagement, interview, or presentation creates training data for potential deepfakes. Business leaders who maintain public profiles face higher risks, but anyone with a recorded speech becomes vulnerable. Even customer service calls provide sufficient audio for basic voice cloning.
Detection challenges multiply with audio deepfakes. Visual deepfakes leave artefacts—unusual eye movements, inconsistent lighting, or temporal anomalies. Audio deepfakes lack these visible tells. Without specialised tools, even experts struggle to distinguish real from synthetic speech. This detection difficulty makes audio deepfakes particularly dangerous for phone-based business operations.
Text-Based Deepfakes: The Overlooked Danger
Written deepfakes receive less attention but pose significant threats. AI systems trained on someone’s writing style can generate convincing emails, social media posts, or documents that perfectly mimic their communication patterns. These text-based forgeries require no technical expertise to create, yet prove devastating when deployed strategically.
Large language models analyse writing samples to understand individual communication styles. They learn vocabulary preferences, sentence structures, punctuation habits, and rhetorical patterns. Fed sufficient training data—publicly available emails, social media posts, or published articles—these systems generate new content indistinguishable from authentic communications.
Business communications become weaponised through text deepfakes. Fabricated emails from executives announcing layoffs, policy changes, or controversial decisions spread panic before verification occurs. Fake customer testimonials damage competitor reputations. Synthetic negative reviews flood review platforms faster than moderation systems can respond.
Social media amplifies text-based deepfake impact. A single fabricated tweet attributed to your company can trigger viral backlash before correction becomes possible. The speed of social media means false statements reach millions while your legal team is still drafting responses. Retractions rarely achieve the reach of the original false content.
Documentation forgery through AI extends beyond simple text generation. Systems create entire documents—contracts, financial reports, internal memos—that appear authentic. These forgeries include appropriate formatting, corporate language, and even realistic metadata. Detecting these sophisticated forgeries requires forensic analysis most businesses can’t perform quickly enough to prevent damage.
Current Deepfake Detectors: Your Essential Defence Arsenal

Modern deepfake detectors employ sophisticated algorithms to identify synthetic content across multiple media types. Understanding these detection capabilities and limitations helps businesses build comprehensive defensive strategies.
Computer Vision Detection Systems
Intel’s FakeCatcher represents current state-of-the-art visual deepfake detection, claiming 96% accuracy in real-time analysis. The system analyses blood flow patterns in faces, detecting subtle colour changes invisible to human eyes but present in real videos. Deepfakes can’t replicate these physiological signals because they’re generated from static images rather than living subjects.
Microsoft’s Video Authenticator provides accessibility-focused detection for businesses. The tool analyses videos and images, providing confidence scores indicating manipulation likelihood. Integration with Microsoft’s broader security ecosystem enables enterprise-wide deployment, protecting organisations from deepfake threats across communication channels.
Google’s Synthid watermarks AI-generated content at creation, enabling later verification. While this approach only works for content created using Google’s tools, it represents an important shift toward provenance tracking. As more platforms adopt similar approaches, distinguishing legitimate from synthetic content becomes easier.
Facebook’s Deepfake Detection Challenge produced multiple detection algorithms that are now available open-source. These tools use various approaches—analysing temporal inconsistencies, detecting generation artefacts, and identifying impossible lighting conditions. Running multiple detection algorithms simultaneously improves accuracy beyond any single tool’s capabilities.
Academic institutions contribute cutting-edge detection research. MIT’s PhotoGuard prevents AI from manipulating images by adding imperceptible perturbations that confuse generation algorithms. While not detecting existing deepfakes, such protective technologies prevent your legitimate content from being weaponised against you.
Audio Analysis Platforms
Resemble AI‘s Resemble Detect identifies synthetic speech across multiple generation methods. The system analyses spectral patterns, identifying artefacts introduced during synthesis. Real-time processing enables integration with phone systems, protecting against voice cloning fraud during live calls.
Pindrop‘s voice authentication technology goes beyond simple detection, creating voiceprints for authorised speakers. Any deviation from established voice patterns triggers alerts, whether from deepfakes or human impersonators. This proactive approach prevents unauthorised actions rather than just detecting them after the fact.
Reality Defender offers comprehensive media authentication, analysing audio, video, and images simultaneously. The platform’s API enables integration with existing content management systems, automatically scanning uploaded media for manipulation. This automated approach scales detection across large content volumes without manual review.
Deepware Scanner provides free deepfake detection for individuals and small businesses. While less sophisticated than enterprise solutions, it offers accessible protection for resource-constrained organisations. The tool’s browser extension automatically scans videos on social media platforms, alerting users to potential deepfakes.
Speech pattern analysis extends beyond voice characteristics to communication patterns. These systems identify linguistic anomalies—unusual word choices, atypical sentence structures, or inconsistent speaking patterns that suggest synthetic generation. Combined with voice analysis, linguistic assessment significantly improves detection accuracy.
Blockchain Verification Systems
Content Authenticity Initiative, led by Adobe, creates tamper-evident records of content creation and editing. Every modification gets recorded in blockchain ledgers, creating immutable provenance chains. Viewers can verify content hasn’t been manipulated since creation, though this requires adoption across creation tools and platforms.
Numbers Protocol embeds ownership and authenticity information directly into media files. Their blockchain-based approach ensures content attribution remains attached regardless of sharing or reposting. For businesses protecting brand assets, this technology provides legal evidence of ownership and originality.
Truepic captures and verifies photos and videos at the point of creation. Their technology combines blockchain provenance with cryptographic signatures, creating unforgeable proof of authenticity. Insurance companies, news organisations, and legal firms increasingly require Truepic verification for submitted media.
RKVST provides supply chain verification that extends to digital content. Originally designed for physical goods tracking, their blockchain platform now tracks digital asset creation, modification, and distribution. This approach treats content like physical products, maintaining chain-of-custody documentation throughout its lifecycle.
Smart contracts automate authenticity verification, triggering actions based on content provenance. Platforms could automatically reject unverified content, payment systems could require authenticated media for transactions, or social networks could label content based on verification status. These automated systems scale protection beyond manual verification capabilities.
Brand Protection Strategies in the Deepfake Era
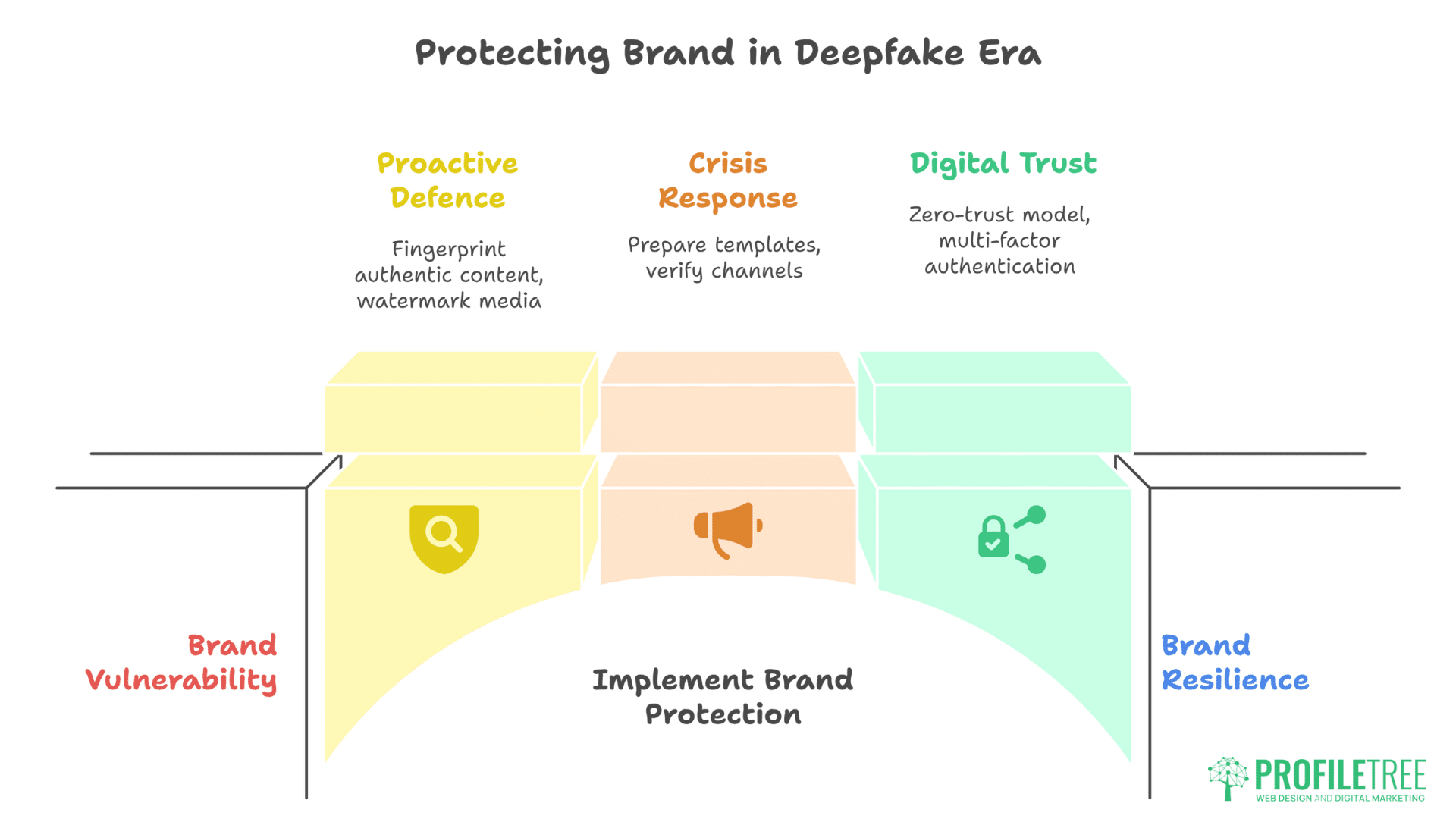
Effective brand protection requires combining deepfake detectors with proactive defensive measures that prevent attacks and enable rapid response when synthetic content emerges targeting your business.
Proactive Defence Measures
Digital fingerprinting your authentic content creates verifiable baselines for comparison. Document all official videos, images, and audio with cryptographic signatures, timestamps, and blockchain records. When deepfakes emerge, you can definitively prove what’s real versus fabricated. This preparation transforms crisis response from desperate denial to confident refutation.
Watermarking strategies must evolve beyond visible logos. Implement stenographic watermarks—invisible markers embedded in media that survive compression and editing. These hidden signatures prove content origin without affecting viewer experience. Modern watermarking survives social media reposting, screenshot capture, and even some editing operations.
Create “proof of life” protocols for executive communications. Establish verification methods for important announcements—perhaps specific phrases, visual elements, or distribution channels that authenticate genuine messages. Train stakeholders to expect and check these verification elements before accepting significant communications as legitimate.
Media asset management requires military-grade security. Every photo, video, or audio file represents potential deepfake training data. Implement access controls, audit trails, and encryption for all media assets. Remove unnecessary content from public platforms—old executive interviews or employee photos that could enable deepfake creation.
Regular security audits should include deepfake vulnerability assessments. Evaluate what content exists publicly about key personnel. Assess communication channels for impersonation risks. Test detection tools against synthetic content mimicking your brand. These audits reveal vulnerabilities before attackers exploit them.
Crisis Response Frameworks
Speed determines outcome in deepfake crises. Prepare response templates, decision trees, and communication protocols before attacks occur. The first hours after a deepfake release determine whether truth or fiction dominates the narrative. Prepared organisations respond in minutes while unprepared ones spend hours in panicked meetings.
Establish verification channels that audiences trust for authentic communications. This might include verified social media accounts, specific website sections, or email lists. Promote these channels before crises occur so audiences know where to find truthful information when deepfakes spread.
Legal response teams need deepfake expertise. Traditional defamation approaches prove insufficient against synthetic media. Lawyers must understand technology, evidence preservation requirements, and platform-specific takedown procedures. Pre-crisis legal preparation saves critical hours when attacks occur.
Platform relationships matter during crisis response. Establish contacts at major social media platforms, understand their deepfake policies, and document verification requirements. Platforms respond faster to prepared organisations presenting clear evidence than panicked businesses making vague complaints.
Employee communication protocols prevent internal chaos. Staff discovering deepfakes about their company naturally panic, potentially amplifying false narratives through well-intentioned responses. Clear protocols about who speaks publicly, how to report suspected deepfakes, and what information to share internally prevent employee actions from worsening situations.
Building Digital Trust Architecture
Zero-trust security models extend to content verification. Assume all media is potentially fake until proven otherwise. This mindset shift from default trust to default scepticism protects against sophisticated deepfakes that fool casual observation.
Multi-factor authentication for content proves more reliable than single verification methods. Combine blockchain provenance, cryptographic signatures, and detection algorithms. When multiple verification methods agree, confidence in authenticity increases exponentially. Professional web development incorporates these authentication layers into your digital infrastructure.
Transparency about AI use builds audience trust before crises occur. If you use AI for marketing, declare it openly. Establish clear boundaries between AI-assisted and human-generated content. This transparency creates credibility reserves you can draw upon when distinguishing real from fake becomes critical.
Community verification harnesses collective intelligence. Encourage customers, employees, and partners to report suspected deepfakes. Create simple reporting mechanisms and response protocols. Communities often detect subtle anomalies that automated systems miss, providing early warning of emerging threats.
Trust tokens create persistent identity verification across platforms. These cryptographic credentials prove account authenticity without revealing personal information. As platforms adopt trust token standards, verified businesses gain protection against impersonation while maintaining privacy.
Industry-Specific Vulnerabilities and Solutions
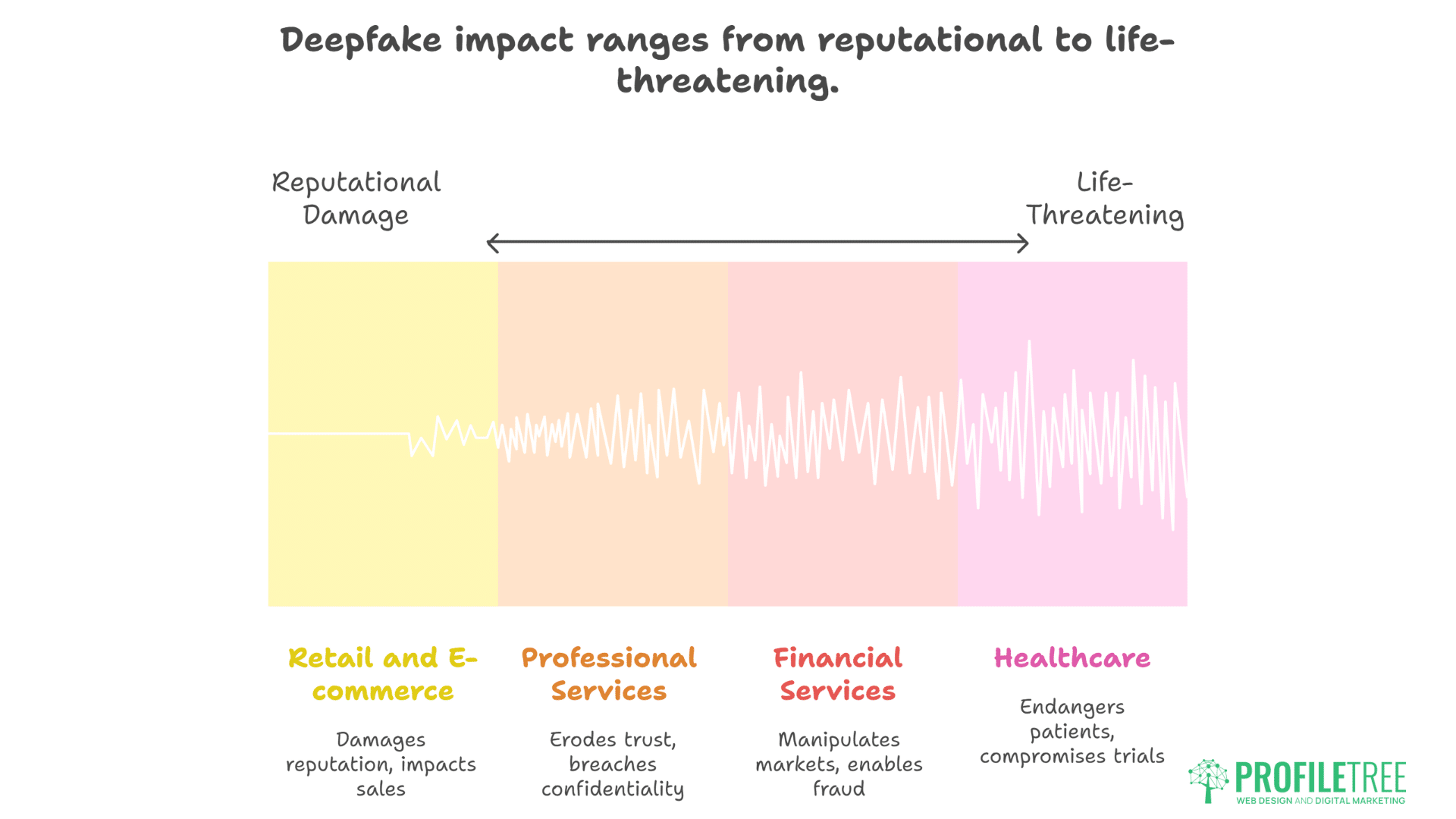
Different industries face unique deepfake threats requiring tailored defensive approaches that combine industry-specific deepfake detectors with sector-appropriate protective strategies and response protocols.
Financial Services: The Prime Target
Banks and financial institutions face existential threats from deepfake technology. Voice cloning enables unauthorised transaction approvals. Fake executive videos manipulate stock prices. Synthetic customer complaints damage carefully built reputations. The financial sector’s dependence on trust makes it particularly vulnerable to deepfake attacks.
Know Your Customer (KYC) protocols require fundamental redesign for deepfake threats. Traditional identity verification—photo IDs, video calls, voice recognition—becomes unreliable when any media can be faked. Multi-modal biometric verification combining multiple unpredictable factors provides stronger protection than single authentication methods.
Trading floor implications extend beyond individual fraud to market manipulation. Deepfake videos of central bankers, CEOs, or analysts making market-moving statements could trigger algorithmic trading cascades before human verification occurs. Microsecond trading decisions based on false information could cause flash crashes or wealth transfers.
Insurance complications multiply as deepfakes blur claim verification. How do insurers verify accident footage when any video could be synthetic? How do they investigate fraud when evidence itself becomes suspect? The insurance industry must develop new verification frameworks or risk either massive fraud losses or legitimate claim denials.
Regulatory compliance adds complexity to the deepfake response. Financial regulations require preserving communications, but what happens when those communications include deepfakes? How do firms prove compliance when regulators might receive synthetic evidence? These questions require regulatory framework updates addressing synthetic media reality.
Retail and E-commerce: Reputation Warfare
Online retailers face deepfake threats across multiple vectors. Fake product videos show items failing catastrophically. Synthetic customer testimonials destroy trust. Fabricated executive statements about quality issues trigger boycotts. The speed of e-commerce means reputational damage immediately translates to lost sales.
Product demonstration videos become weapons when deepfaked. Competitors or malicious actors create videos showing products causing injuries, failing safety tests, or performing poorly. These videos spread through social media faster than fact-checkers can respond. Small businesses lack resources for rapid response, suffering disproportionate damage.
Customer review systems already struggle with fake text reviews—deepfake video reviews exponentially compound this problem. A synthetic video review appears more credible than text, carrying greater influence over purchasing decisions. Platforms lack tools to verify video review authenticity at scale.
Influencer marketing faces existential challenges when any endorsement could be faked. Brands can’t verify whether influencers actually made statements attributed to them. Influencers can’t prove they didn’t make controversial statements. This uncertainty undermines the entire influencer marketing ecosystem.
Supply chain verification becomes critical as deepfakes enable sophisticated fraud. Fake videos of warehouse fires, shipping delays, or quality control failures manipulate supply chain decisions. Companies make expensive contingency plans based on false information, disrupting operations and increasing costs.
Healthcare: Life-and-Death Implications
Medical deepfakes pose unique dangers because healthcare decisions carry life-or-death consequences. Fake videos of doctors providing medical advice. Synthetic testimonials about treatment outcomes. Fabricated pharmaceutical announcements about drug safety. These deepfakes don’t just damage reputations—they threaten patient safety.
Telemedicine vulnerabilities multiply with real-time deepfake capabilities. How can patients verify they’re consulting real doctors? How can doctors confirm patient identities for prescription purposes? The rapid telemedicine expansion during COVID-19 created attack surfaces that deepfake technology exploits.
Medical training using synthetic patients raises ethical questions. While deepfakes could create valuable training scenarios, they also risk desensitising medical professionals to human suffering. The line between beneficial simulation and problematic dehumanisation requires careful consideration.
Clinical trial integrity faces threats from synthetic evidence. Deepfaked patient testimonials could support or undermine trial results. Fabricated adverse event videos could halt promising treatments. The scientific method depends on truthful data—deepfakes poison this foundation.
Insurance fraud through medical deepfakes represents an emerging threat. Synthetic evidence of injuries, illnesses, or treatments could support fraudulent claims. Conversely, legitimate claimants might face denials because insurers suspect deepfake evidence. This uncertainty increases costs for everyone.
Professional Services: Trust as Currency
Law firms, consultancies, and agencies trade on reputation and expertise. Deepfakes directly attack these foundations. A fabricated video of lawyers discussing cases unethically. Synthetic recordings of consultants revealing client secrets. Fake testimonials about poor service quality. Professional services firms face existential threats from believable false content.
Client confidentiality becomes harder to maintain when deepfakes enable false breach claims. How do firms prove they didn’t say something when synthetic evidence suggests otherwise? Traditional confidentiality protections assume truthful evidence—deepfakes invalidate this assumption.
Expert testimony in legal proceedings faces credibility challenges. If any video can be faked, how do courts evaluate expert evidence? The legal system’s dependence on witness credibility crumbles when technology makes anyone say anything convincingly.
Recruitment and hiring practices must account for deepfake capabilities. Candidates might submit deepfaked references, qualifications, or portfolio work. Conversely, employers might create synthetic evidence to justify discriminatory decisions. Digital training services help HR teams identify and prevent deepfake fraud in hiring processes.
Partnership due diligence requires new verification methods. Traditional background checks assume documentary evidence is genuine. When any document, video, or testimony could be synthetic, due diligence must evolve beyond document review to active verification.
Legal and Regulatory Landscape
Current legislation provides limited protection against deepfake attacks, making business-level defensive measures, including reliable deepfake detectors, essential for protecting against synthetic media threats.
Current UK Legislation
The UK’s Online Safety Act addresses some deepfake concerns but lacks specific synthetic media provisions. The legislation focuses on platform responsibilities for harmful content but doesn’t adequately define “harmful” regarding deepfakes. This regulatory gap leaves businesses vulnerable while lawmakers struggle to understand rapidly evolving technology.
Intellectual property law provides limited deepfake protection. Copyright covers specific expressions but not voices, mannerisms, or likeness in UK law. Trademark protection might apply to corporate imagery but not individual representation. These gaps mean businesses can’t rely on IP law for deepfake protection.
Criminal law adaptations lag behind deepfake capabilities. Fraud statutes might apply to financial deepfake crimes, but reputational attacks fall into grey areas. Harassment laws might cover targeted deepfake campaigns but not isolated incidents. Prosecutors struggle to apply analogue laws to digital crimes.
Data protection regulations offer unexpected deepfake relevance. GDPR requires consent for processing biometric data—including face and voice information used in deepfakes. Businesses might pursue deepfake creators for unauthorised biometric data processing, though enforcement remains untested.
Civil remedies prove expensive and uncertain. Defamation suits require proving falsity and damage—complicated when deepfakes appear genuine. Injunction procedures move slowly while deepfakes spread rapidly. Legal costs often exceed recoverable damages, making civil action economically unviable for small businesses.
International Regulatory Approaches
The EU’s AI Act includes specific deepfake provisions requiring disclosure of synthetic content. Platforms must implement detection systems and label AI-generated media. These requirements create compliance obligations for UK businesses operating in EU markets, regardless of UK regulations.
China mandates deepfake labelling and prohibits synthetic content without subject consent. These strict regulations protect against malicious deepfakes but also restrict legitimate uses. UK businesses operating in China must understand these restrictions or risk severe penalties.
United States approaches vary by state, creating a complex compliance landscape. California requires disclosure of synthetic content in political contexts. Texas criminalises non-consensual intimate deepfakes. Federal legislation remains stalled, leaving a patchwork of state regulations.
International cooperation mechanisms remain underdeveloped. Deepfake creators operate across borders, exploiting jurisdictional gaps. Without international agreements on investigation, prosecution, and platform responsibilities, enforcement remains ineffective against determined attackers.
Industry self-regulation fills some gaps but lacks teeth. The Partnership on AI’s synthetic media framework provides guidelines but no enforcement. Platform policies vary widely and change frequently. Self-regulation helps responsible actors but doesn’t stop malicious ones.
Preparing for Regulatory Evolution
Compliance frameworks must anticipate future regulations. Build systems assuming stricter requirements are coming. Implement authentication, provenance tracking, and disclosure mechanisms now rather than scrambling when regulations arrive.
Documentation strategies should assume litigation. Preserve evidence of content authenticity, deepfake detection efforts, and response actions. Detailed documentation proves good faith efforts even if outcomes prove imperfect.
Insurance considerations require careful evaluation. Current policies might exclude deepfake-related losses. Specific synthetic media coverage remains rare and expensive. Understanding coverage gaps helps prioritise protective investments.
International business requires multi-jurisdictional compliance. Operating across borders means respecting various deepfake regulations. Design global compliance frameworks rather than country-specific patches. This approach ensures protection regardless of regulatory evolution.
Advocacy and education shape future regulations. Engage with policymakers to ensure regulations protect legitimate businesses without stifling innovation. Share real-world impacts to inform evidence-based policy. Professional digital strategy consultation helps navigate evolving regulatory requirements.
Building Organisational Resilience

Organisational resilience against deepfake threats requires combining technological solutions like deepfake detectors with human training, process improvements, and cultural changes to create comprehensive protection frameworks.
Employee Training and Awareness
Staff represent both vulnerability and defence against deepfakes. Employees with public profiles provide training data for deepfakes. Conversely, trained employees detect and report suspicious content before it spreads. Comprehensive training transforms staff from targets into guardians.
Detection training goes beyond technical education to behavioural observation. Teach employees to notice communication anomalies—unusual requests, atypical language, or suspicious urgency. These human insights often catch sophisticated deepfakes that fool technical systems.
Response protocols must be simple and memorable. Complex procedures fail during crisis stress. Create clear escalation paths, designated responders, and simple decision trees. Regular drills ensure employees react appropriately when real threats emerge.
Social engineering awareness becomes critical as deepfakes enable sophisticated attacks. Voice cloning makes phone-based social engineering more convincing. Video deepfakes enable impersonation during video calls. Training must address these evolving threats.
Personal security education protects employees from becoming deepfake targets. Teach staff about public information management, social media privacy, and content sharing risks. Personal security directly impacts corporate security when employees become deepfake training data.
Technical Infrastructure Hardening
Authentication systems require a fundamental redesign for deepfake threats. Multi-factor authentication must use factors that are difficult to deepfake—hardware tokens, behavioural biometrics, or challenge-response protocols. Password-plus-SMS proves insufficient when voices can be cloned.
Communication verification adds friction but prevents catastrophe. Implement callback procedures for sensitive requests. Require multiple approvals for significant actions. Add verification codes to important communications. These measures slow operations slightly but prevent devastating fraud.
Content management systems need authentication layers. Every upload should include provenance information. Every modification should be logged. Every distribution should be tracked. These audit trails prove invaluable when investigating suspected deepfakes.
Network segmentation limits deepfake impact. Isolate critical systems from general communications. Restrict access based on need rather than convenience. Compartmentalisation ensures single deepfake successes don’t compromise entire organisations.
Backup and recovery planning must account for reputational damage. Technical backups restore data but not trust. Prepare communication templates, stakeholder lists, and response procedures. Test recovery procedures, including public relations aspects, not just technical restoration.
Monitoring and Early Warning Systems
Social media monitoring catches emerging deepfakes before viral spread. Automated systems track mentions, analyse sentiment, and flag anomalies. Early detection enables rapid response before false narratives solidify. Quick action often prevents minor incidents from becoming major crises.
Dark web surveillance identifies planned attacks before execution. Criminals often discuss or sell deepfake services on underground forums. Monitoring these spaces provides advanced warning of potential threats. Forewarned organisations can prepare defences or preempt attacks.
Industry intelligence sharing multiplies defensive capabilities. When one company faces deepfake attacks, others in the industry become targets. Sharing threat intelligence helps entire sectors defend against common threats. Collaborative defence proves more effective than isolated responses.
Customer feedback channels often provide the first warning of deepfakes. Customers might ask about controversial videos or express confusion about conflicting messages. These queries signal potential deepfake activity requiring investigation. Training customer service teams to recognise and escalate these signals improves detection speed.
Technical indicators complement human observation. Unusual traffic patterns, authentication failures, or communication anomalies might indicate deepfake activity. Correlating technical and human intelligence improves detection accuracy.
Cost-Benefit Analysis of Protection Measures
Investment in deepfake detectors and comprehensive protection measures requires careful cost-benefit analysis that considers both direct expenses and potential losses from successful synthetic media attacks.
Direct Investment Requirements
Detection technology costs vary dramatically by sophistication. Basic detection tools cost hundreds monthly, while enterprise platforms cost thousands. API-based detection services charge per scan, making costs proportional to content volume. Budget 0.5-2% of revenue for comprehensive detection capabilities.
Training investments deliver multiplicative returns. Initial employee training might cost £500-2000 per session, but prevents losses orders of magnitude larger. Regular refreshers maintain vigilance as threats evolve. Consider training investments insurance premiums against reputational catastrophe.
Infrastructure hardening requires both capital and operational investment. Authentication system upgrades, monitoring platform deployment, and verification process implementation require upfront investment plus ongoing maintenance. These costs pale compared to potential fraud losses or reputational damage.
Legal preparation prevents expensive scrambling during crises. Retaining law firms with deepfake expertise, preparing response procedures, and establishing platform relationships requires investment but saves critical time when attacks occur. Pre-crisis preparation costs a fraction of crisis response.
Insurance premiums for synthetic media coverage remain expensive where available. Premiums range from 0.1-0.5% of coverage amounts, with high deductibles and numerous exclusions. Self-insurance through strong defences often proves more economical than commercial coverage.
Return on Investment Calculations
Prevented losses dwarf protection costs. Single successful deepfake attacks cost businesses average £300,000 in response costs, lost revenue, and reputational repair. Comprehensive protection costing £50,000 annually pays for itself, preventing a single incident.
Competitive advantages accrue to prepared organisations. While competitors scramble with deepfake crises, protected businesses maintain operations and capture market share. Trust becomes a competitive differentiator when authenticity grows scarce.
Customer confidence translates to revenue. Businesses demonstrating strong authentication and verification build trust that converts to sales. Surveys show 73% of consumers prefer businesses with visible security measures. This preference intensifies as deepfake awareness grows.
Operational efficiency improves through an authentication infrastructure. Systems built for deepfake protection also prevent traditional fraud, improve communication security, and streamline verification processes. These auxiliary benefits often justify investment independently.
Brand value preservation represents incalculable returns. Reputation takes years to build but minutes to destroy. Deepfake protection preserves intangible assets worth multiples of protection costs. For many businesses, brand value exceeds all tangible assets combined.
Resource Allocation Strategies
Prioritise protection based on risk assessment. Public-facing executives need more protection than back-office staff. Customer-facing channels require stronger authentication than internal communications. Financial processes demand the highest security levels. Allocate resources proportional to risk.
Phase implementation based on immediate threats and available resources. Start with employee training and basic detection tools. Add authentication systems and monitoring platforms as budgets allow. Build toward comprehensive protection through incremental improvements rather than waiting for perfect solutions.
Leverage free and low-cost tools before premium investments. Open-source detection algorithms, platform-provided verification tools, and community intelligence provide meaningful protection without significant cost. Combine multiple free tools rather than relying on a single expensive platform.
Partner with other organisations for shared defence. Industry associations, local business groups, or supply chain partners can share threat intelligence, split monitoring costs, or coordinate responses. Collective defence multiplies individual investments.
Balance prevention, detection, and response investments. Preventing all deepfakes proves impossible, so invest in rapid detection and effective response alongside prevention. Diversified defence proves more resilient than single-point solutions.
Future-Proofing Your Digital Trust Strategy

As deepfake technology evolves, businesses must anticipate how deepfake detectors and defensive strategies will need to adapt to maintain effective protection against increasingly sophisticated threats.
Emerging Technologies and Threats
Quantum computing threatens current cryptographic protections. Authentication systems relying on traditional encryption become vulnerable to quantum attacks. Organisations must prepare for post-quantum cryptography migration before quantum computers become widely available.
Generative AI advancement accelerates beyond detection capabilities. Each AI generation produces more convincing deepfakes while detection lags behind. Prepare for periods when detection proves impossible, requiring alternative verification methods.
Real-time deepfakes evolve toward perfect impersonation. Current processing delays and quality limitations disappear as technology advances. Prepare for a world where any real-time communication could be synthetic without detection possibilities.
Synthetic reality extends beyond media to entire digital experiences. Deepfaked websites, documents, and databases create alternative realities indistinguishable from truth. Verification must extend beyond media to entire digital environments.
Biological deepfakes might synthesise DNA evidence, fingerprints, or other biometric data. Current biometric authentication assumes biological uniqueness—synthetic biology invalidates these assumptions. Authentication must evolve beyond biological factors.
Strategic Adaptation Frameworks
Continuous learning organisations survive technological disruption. Establish processes for monitoring emerging threats, evaluating new defences, and updating procedures. Static security fails against evolving threats—adaptation ensures survival.
Scenario planning prepares for various futures. Develop response plans for different deepfake evolution paths. What if detection becomes impossible? What if creation becomes trivial? What if regulations ban synthetic media entirely? Prepared organisations adapt faster to whatever future emerges.
Innovation partnerships accelerate defensive capabilities. Collaborate with universities researching detection methods. Partner with technology companies developing authentication systems. Engage with startups creating novel solutions. External innovation supplements internal capabilities.
Cultural evolution toward healthy scepticism protects against future threats. Foster organisational cultures that question, verify, and authenticate rather than assuming truth. This cultural shift provides protection regardless of technological evolution.
Investment in fundamental trust infrastructure pays dividends regardless of specific threats. Strong authentication, comprehensive monitoring, and rapid response capabilities protect against current deepfakes and unknown future threats. AI training services help organisations build adaptive capabilities for evolving threats.
Practical Implementation Roadmap
Systematic implementation of deepfake detectors and protective measures requires phased approaches that build comprehensive defence capabilities while managing costs and operational disruption effectively.
30-Day Quick Wins
Audit your digital footprint to understand existing vulnerabilities. Catalogue public content featuring key personnel. Identify high-risk communication channels. Document current authentication procedures. This baseline assessment reveals immediate improvement opportunities.
Implement basic employee training covering deepfake awareness and reporting procedures. Two-hour sessions provide a sufficient introduction without overwhelming staff. Focus on recognition and response rather than technical details. Simple awareness dramatically improves organisational resilience.
Deploy free detection tools as first-line defence. Browser extensions, online scanners, and platform-provided tools offer immediate protection without investment. While imperfect, these tools catch obvious deepfakes that might otherwise spread unchecked.
Establish verification protocols for sensitive communications. Implement callback procedures for financial requests. Require multiple approvals for public statements. Add authentication codes to executive communications. These simple measures prevent most deepfake-enabled fraud.
Create response templates for potential deepfake scenarios. Draft statements for various attack types. Identify spokesperson and approval chains. Document platform contact information. Preparation transforms panic into process when attacks occur.
90-Day Foundation Building
Develop comprehensive deepfake response plans covering detection, verification, communication, and recovery. Include decision trees, escalation procedures, and stakeholder responsibilities. Test plans through tabletop exercises, identifying gaps and improvements.
Upgrade authentication systems to multi-factor methods resistant to deepfake attacks. Implement hardware tokens, behavioural biometrics, or challenge-response protocols. Phase rollout starting with the highest-risk processes, then expanding coverage.
Establish monitoring systems for early deepfake detection. Deploy social media monitoring, implement Google Alerts, and subscribe to threat intelligence feeds. Early warning enables rapid response before viral spread.
Build relationships with key platforms and service providers. Establish contacts at social media companies, understand takedown procedures, and document verification requirements. These relationships prove invaluable during crisis response.
Begin content authentication initiatives. Implement watermarking, establish provenance tracking, deploy blockchain verification where appropriate. These measures create verifiable baselines distinguishing real from fake content.
Six-Month Maturity Targets
Achieve comprehensive protection across all major vulnerability points. Detection systems operate continuously. Authentication protects all critical processes. Response procedures tested and refined. Monitoring provides early warning of emerging threats.
Integrate deepfake defence into broader risk management frameworks. Regular risk assessments, including deepfake threats. Business continuity plans accounting for reputational attacks. Insurance coverage addressing synthetic media risks where available.
Establish industry collaboration for shared defence. Participate in threat intelligence sharing. Contribute to industry best practices. Coordinate responses to common threats. Collective defence multiplies individual capabilities.
Develop internal expertise, reducing dependence on external resources. Train internal deepfake specialists. Build institutional knowledge about threats and defences. Create sustainable protection independent of vendor changes.
Measure and optimise protection effectiveness. Track detection rates, response times, and prevented incidents. Calculate return on protection investments. Identify improvement opportunities. Continuous optimisation ensures evolving protection against evolving threats.
Frequently Asked Questions
How can small businesses afford deepfake protection when enterprise solutions cost thousands monthly?
Start with free tools and basic training costing under £500. Google’s Synthid, Deepware Scanner, and platform detection features provide meaningful protection without investment. Focus on employee awareness and simple verification protocols that prevent most attacks. Scale up protection as your business grows and threats evolve.
What’s the single most important thing businesses should do to protect against deepfakes?
Implement verification protocols for sensitive communications immediately. Require callbacks for financial requests, multiple approvals for public statements, and authentication codes for executive messages. These simple procedures prevent most deepfake-enabled fraud without expensive technology investments.
How can we detect deepfakes when detection technology lags behind the creation capabilities?
Combine multiple detection methods rather than relying on single solutions. Use technical detection tools, human observation, behavioural analysis, and verification protocols together. Multiple imperfect methods provide better protection than single perfect solutions that don’t exist.
Should we remove all public content to prevent deepfake training?
Complete removal proves impractical and potentially counterproductive. Instead, audit existing content, remove unnecessary high-risk material, and implement authentication for new content. Balance security with business needs rather than choosing extremes.
Which industries face the highest deepfake risks?
Financial services, healthcare, and professional services face extreme risks due to trust dependence. Retail and hospitality suffer from reputational attacks. Manufacturing confronts supply chain manipulation. Every industry faces threats, but impact varies by business model and customer relationships.
How do we respond if a deepfake about our company goes viral?
Speed matters most. Immediately acknowledge awareness, state it’s being investigated, and direct audiences to official channels for updates. Provide clear evidence of falseness through prepared verification methods. Focus on the truth rather than attacking perpetrators. Crisis communication support helps manage the response effectively.
Will deepfake insurance become standard business coverage?
Specific deepfake coverage remains rare and expensive currently. However, cyber insurance increasingly includes synthetic media provisions. As threats grow and actuarial data accumulates, coverage will likely become standard. Meanwhile, focus on prevention rather than insurance.
Can blockchain technology solve the deepfake problem?
Blockchain provides valuable provenance tracking but isn’t a complete solution. It verifies content hasn’t changed since creation but can’t prevent initial deepfake creation. Blockchain forms part of a comprehensive protection rather than a standalone solution.
Take Decisive Action Today
The deepfake threat isn’t coming—it’s here. Every day without protection increases vulnerability to attacks that could destroy your business overnight. But paralysis serves no purpose. Start with simple steps: train your team, implement verification protocols, and deploy free detection tools. Build from this foundation toward comprehensive protection.
Northern Ireland businesses face unique challenges but also unique opportunities. Tight-knit business communities enable rapid intelligence sharing and coordinated defence. Local market knowledge helps distinguish authentic from synthetic content. Cultural understanding provides context that automated systems miss.
ProfileTree helps businesses navigate the deepfake minefield with practical, actionable strategies. Our AI training services equip teams to recognise and respond to synthetic media threats. Our digital strategy consultation integrates deepfake defence into a comprehensive digital transformation. We understand that technology alone doesn’t provide protection—it’s the combination of tools, training, and processes that builds resilience.
Don’t wait for deepfakes to target your business. Preparation today prevents catastrophe tomorrow. The question isn’t whether you’ll face deepfake threats but whether you’ll be ready when they arrive. Make the choice that protects your reputation, your revenue, and your future. Start building your deepfake defence today.