Essential Top Endpoint Protection Software to Safeguard Your Device
Table of Contents
Top Endpoint Protection Software is critical as cyber threats continue to evolve at an alarming rate, targeting organisations of all sizes across Northern Ireland, the UK, and beyond. As business operations become increasingly digital, protecting your company’s endpoints—computers, mobile devices, servers, and IoT devices—has never been more important. These Top Endpoint Protection Software solutions offer comprehensive security against malware, ransomware, and sophisticated cyber attacks that could compromise sensitive business data.
For businesses in Belfast, Dublin, and throughout the UK, implementing robust endpoint security isn’t just good practice—it’s essential for maintaining operational integrity and customer trust. Without proper protection, your organisation remains vulnerable to data breaches that can lead to significant financial losses, regulatory penalties, and irreparable damage to your reputation.
This guide explores the leading Top Endpoint Protection Software options available to businesses, their key features, benefits, and how to select the solution that best aligns with your specific security requirements.
Understanding Endpoint Protection: What You Need to Know

Before diving into specific software solutions, it’s important to understand what endpoint protection actually entails and why it matters for your business.
What is Endpoint Protection?
Endpoint protection refers to the security measures implemented to defend the endpoints or entry points of end-user devices from being exploited by malicious actors and campaigns. These endpoints include desktop computers, laptops, mobile phones, tablets, servers, and IoT devices that connect to your network.
Modern Top Endpoint Protection Software goes beyond traditional antivirus capabilities, offering multi-layered defence mechanisms including:
- Real-time threat detection and prevention
- Behavioural analysis to identify suspicious activities
- Application control and whitelisting
- Data loss prevention
- Endpoint detection and response (EDR)
- Network protection
- Vulnerability assessment and patch management
Why Businesses Need Robust Endpoint Security
The shift to remote and hybrid work models has significantly expanded the attack surface for many organisations. With employees accessing company resources from various locations and devices, traditional network perimeter security is no longer sufficient.
According to recent data, endpoints are involved in 70% of successful breaches, making them prime targets for cybercriminals. For businesses in Northern Ireland and across the UK, the consequences of inadequate endpoint security can be severe:
- Financial losses from operational disruption and ransom payments
- Compliance violations leading to substantial fines under GDPR
- Theft of intellectual property and sensitive business data
- Damage to customer relationships and brand reputation
“The evolution of cyber threats means that basic antivirus solutions are no longer adequate for business security,” says Ciaran Connolly, Director at ProfileTree. “Modern enterprises require intelligent Top Endpoint Protection Software that can adapt to emerging threats and provide comprehensive visibility across all connected devices.”
Top Endpoint Protection Software Solutions for 2025

When evaluating Top Endpoint Protection Software for your organisation, consider these leading solutions that have demonstrated exceptional performance in protecting business endpoints.
CrowdStrike Falcon
CrowdStrike Falcon has established itself as one of the premier endpoint protection platforms, particularly for mid-sized to enterprise organisations. Its cloud-native architecture eliminates the need for on-premises servers and reduces the performance impact on protected devices.
Key Features:
- AI-powered threat detection and prevention
- Real-time visibility and comprehensive EDR capabilities
- 24/7 managed threat hunting
- Integration with intelligence feeds for emerging threat protection
- Minimal system impact with cloud delivery model
CrowdStrike’s strength lies in its ability to detect and respond to threats using behavioural analysis rather than relying solely on signature-based detection. This makes it particularly effective against zero-day exploits and fileless malware that traditional solutions might miss.
Microsoft Defender for Endpoint
Formerly known as Microsoft Defender ATP, this solution has evolved significantly to become a robust option, especially for organisations already invested in the Microsoft ecosystem.
Key Features:
- Deep integration with Windows and Microsoft 365
- Advanced EDR capabilities with automated investigation and remediation
- Threat and vulnerability management
- Attack surface reduction rules
- Seamless deployment for Microsoft customers
For businesses in Belfast and across the UK using Microsoft environments, Defender for Endpoint offers the advantage of unified management through Microsoft security portals, simplifying administration and reducing operational complexity.
SentinelOne Singularity Platform
SentinelOne has gained recognition for its autonomous approach to endpoint protection, using sophisticated AI algorithms to detect and respond to threats with minimal human intervention.
Key Features:
- Autonomous detection and response capabilities
- Rollback functionality to restore affected systems
- Cross-platform protection (Windows, macOS, Linux)
- One-click remediation options
- Detailed forensic analysis
SentinelOne’s ability to automatically remediate threats makes it particularly valuable for organisations with limited security personnel. Its effectiveness against ransomware—with the ability to roll back systems to pre-infection states—provides an additional layer of protection that many competing solutions lack.
Sophos Intercept X
Sophos Intercept X combines endpoint protection with EDR capabilities, offering strong protection against a wide range of threats, including ransomware and exploit-based attacks.
Key Features:
- Deep learning AI for malware detection
- Anti-ransomware capabilities
- Exploit prevention
- Managed threat response option
- Cloud-based management console
Sophos is known for its user-friendly interface and clear security reporting, making it accessible for small and medium-sized businesses without dedicated security teams. Its ransomware-specific protections, including the ability to recover encrypted files, make it particularly valuable in the current threat landscape.
Trend Micro Apex One
Trend Micro’s flagship endpoint security solution offers comprehensive protection against file and fileless threats through its connected threat defence approach.
Key Features:
- Virtual patching for vulnerability protection
- Advanced threat scanning and sandbox analysis
- Behavioural analysis and machine learning detection
- Centralised management console
- Data loss prevention capabilities
Apex One’s strength lies in its hybrid approach, combining cloud-based intelligence with local detection capabilities to maintain protection even when devices are offline. Its virtual patching feature helps mitigate risks from unpatched vulnerabilities, addressing a common security gap for many businesses.
Bitdefender GravityZone
Bitdefender GravityZone consistently ranks among the Top Endpoint Protection Software solutions for its excellent malware detection rates and low system impact.
Key Features:
- Machine learning and behaviour-based detection
- Risk analytics and hardening recommendations
- Network attack defence
- Advanced anti-exploit techniques
- Integrated patch management
Bitdefender’s multi-layered approach combines traditional signature-based detection with advanced techniques like machine learning and sandboxing. This comprehensive strategy helps it achieve consistently high detection rates in independent tests while maintaining good system performance.
ESET Endpoint Security
ESET offers lightweight endpoint protection with a strong focus on detection capabilities and system performance.
Key Features:
- Low system footprint
- Network attack protection
- Advanced memory scanner
- Exploit blocker
- Cloud-based reputation system
ESET’s solutions are particularly popular among small to mid-sized businesses that require strong protection without significant performance impacts. Its management console provides good visibility across protected endpoints while remaining accessible to IT generalists.
Key Features to Look for in Top Endpoint Protection Software

When evaluating Top Endpoint Protection Software for your organisation, consider these essential features that differentiate leading solutions:
Real-Time Threat Detection and Prevention
Modern endpoint protection must provide real-time monitoring and immediate response to suspicious activities. Look for solutions that use advanced detection methods, including:
- Machine learning algorithms
- Behavioural analysis
- Heuristic scanning
- Reputation services
These technologies work together to identify both known and unknown threats before they can execute on your systems.
Endpoint Detection and Response (EDR)
EDR capabilities extend traditional endpoint protection by providing:
- Continuous monitoring and recording of endpoint activity
- Advanced threat hunting capabilities
- Detailed forensic information for incident investigation
- Automated response options for common threats
EDR functionality is increasingly essential for organisations looking to not just prevent attacks but understand them when they do occur.
Centralised Management
For businesses managing multiple endpoints across different locations, centralised management is crucial. Look for solutions offering:
- Single-console visibility across all protected devices
- Consistent policy deployment
- Automated reporting capabilities
- Role-based access control for administrative functions
Centralised management reduces operational overhead and ensures a consistent security posture across your organisation.
Cross-Platform Support
Modern business environments typically include a mix of operating systems and device types. Ensure your chosen endpoint protection supports:
- Windows, macOS, and Linux desktops/laptops
- iOS and Android mobile devices
- Virtual environments
- Cloud workloads
Comprehensive coverage prevents security gaps that could arise from inconsistent protection across platforms.
Performance Impact
Effective security shouldn’t come at the cost of system performance. Evaluate the resource requirements of any Top Endpoint Protection Software you’re considering, with particular attention to:
- CPU usage during scans
- Memory footprint
- Impact on boot times
- Effect on common business applications
Many modern solutions optimise performance by leveraging cloud-based analysis and selective scanning techniques.
Integration Capabilities
Security doesn’t exist in isolation. The best endpoint protection solutions offer integration with:
- SIEM (Security Information and Event Management) systems
- Identity and access management solutions
- Network security tools
- Threat intelligence platforms
These integrations create a more cohesive security ecosystem that improves overall protection and streamlines management.
Implementation Best Practices for Top Endpoint Protection Software

Selecting the right Top Endpoint Protection Software is just the first step. Proper implementation is crucial to achieving optimal security benefits for your organisation.
Develop a Clear Deployment Strategy
Before rolling out endpoint protection across your organisation:
- Inventory all endpoints that need protection
- Prioritise critical systems for initial deployment
- Establish a testing protocol for compatibility with business applications
- Create a phased implementation plan to minimise disruption
A structured approach prevents gaps in coverage and reduces the risk of deployment-related issues.
Configure Policies Appropriately
Default security settings rarely provide the optimal balance of protection and usability for specific business environments. Take time to:
- Review default policies and adjust based on your risk profile
- Create role-based security policies for different user groups
- Implement application whitelisting for high-security environments
- Configure data protection rules aligned with compliance requirements
Tailored policies improve security while minimising false positives that could impact productivity.
Establish Monitoring and Response Procedures
Top Endpoint Protection Software generates security alerts that require appropriate handling:
- Define alert severity classifications and corresponding response procedures
- Establish clear responsibilities for monitoring and incident response
- Create escalation paths for significant threats
- Develop documentation for common remediation actions
Well-defined procedures ensure consistent and timely responses to security events.
Conduct Regular Security Assessments
Endpoint security isn’t a “set and forget” solution. Schedule regular reviews to:
- Validate that all endpoints remain protected
- Assess the effectiveness of current security policies
- Identify potential vulnerabilities or misconfigurations
- Incorporate new protection capabilities as they become available
Ongoing assessment helps maintain your security posture as both your business and the threat landscape evolve.
Common Challenges and Solutions with Endpoint Protection
Even with Top Endpoint Protection Software, organisations often face implementation challenges. Here’s how to address the most common issues:
Challenge: User Resistance
Security measures perceived as disruptive to productivity often face user resistance.
Solution:
- Provide clear communication about security measures and their importance
- Offer training on security best practices
- Implement protection in ways that minimise user disruption
- Consider user experience when configuring security policies
User buy-in significantly improves the effectiveness of endpoint protection.
Challenge: Managing Remote Devices
The rise of remote work has complicated endpoint security management.
Solution:
- Implement cloud-based management solutions that don’t require VPN connectivity.
- Establish clear security policies for remote workers
- Use agent-based protection that functions independently of network location
- Consider zero-trust architectures for accessing sensitive resources
Effective protection must extend beyond traditional network boundaries.
Challenge: Resource Limitations
Many organisations, especially SMEs, face resource constraints when implementing comprehensive security.
Solution:
- Consider managed security services for expert oversight
- Prioritise protection for critical systems and sensitive data
- Leverage automated response capabilities to reduce manual intervention
- Choose solutions with good out-of-the-box protection and reasonable default configurations
Strategic deployment helps maximise security benefits with limited resources.
Challenge: Keeping Protection Updated
Outdated security solutions create vulnerabilities as new threats emerge.
Solution:
- Select solutions with automatic updating capabilities.
- Implement patch management as part of your security strategy
- Regularly review vendor threat intelligence and security advisories
- Schedule periodic reassessment of your security toolset
Staying current is essential for maintaining effective protection.
The Future of Endpoint Protection
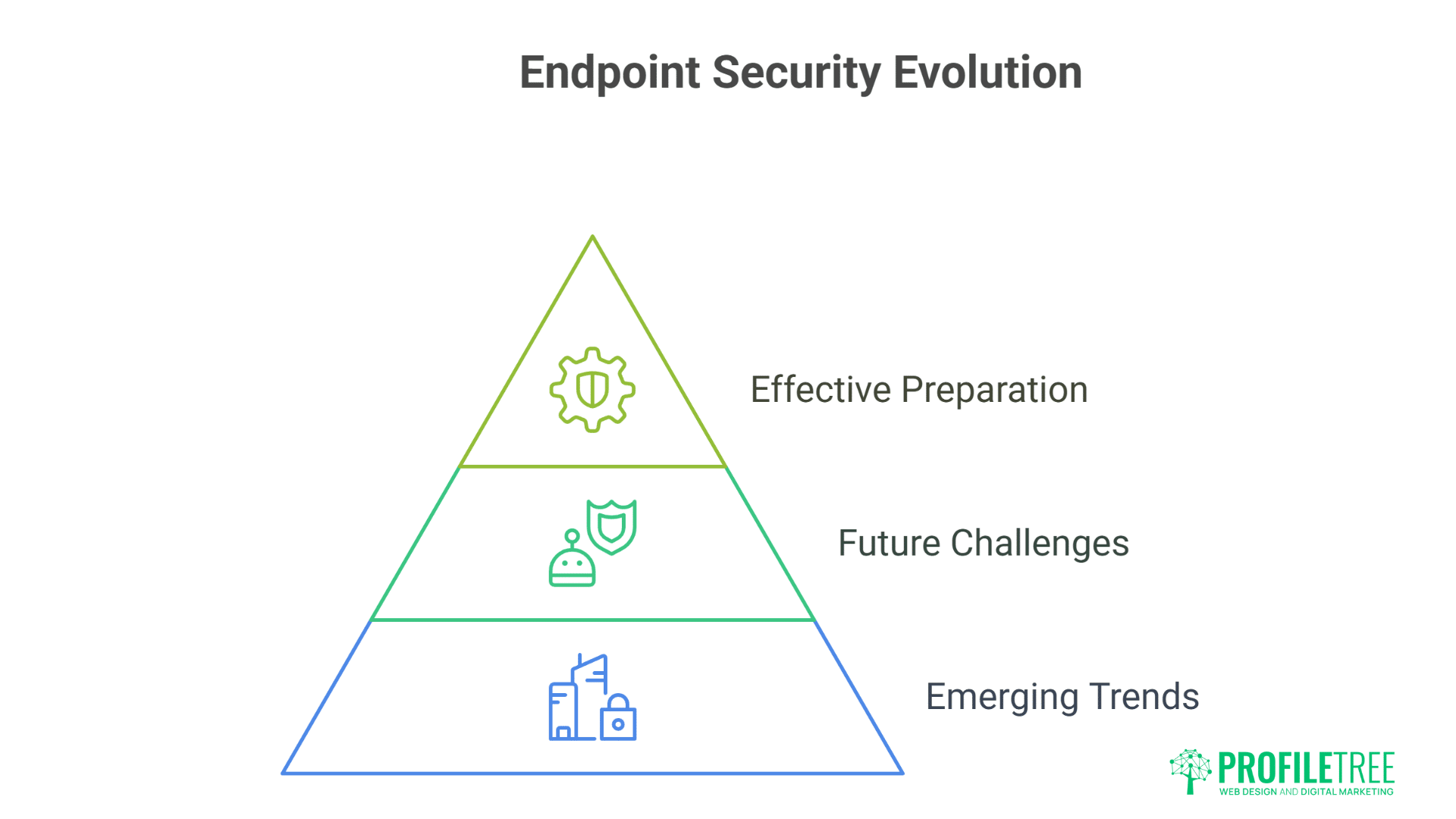
The endpoint security landscape continues to evolve rapidly. Understanding emerging trends helps organisations prepare for future security challenges.
Integration of AI and Machine Learning
AI capabilities in Top Endpoint Protection Software are becoming increasingly sophisticated, offering:
- Improved zero-day threat detection
- Predictive security based on behaviour analysis
- Automated threat hunting and investigation
- Reduced false positives through contextual analysis
These advances enable more effective protection with less human intervention.
Extended Detection and Response (XDR)
XDR represents the evolution of EDR, expanding visibility beyond endpoints to include:
- Network traffic analysis
- Email security
- Cloud workload protection
- Identity management
This holistic approach provides more comprehensive threat detection and response capabilities.
Zero-Trust Security Models
Traditional perimeter-based security continues to give way to zero-trust approaches, where:
- All access requests are verified regardless of source
- Strict access controls apply even within the network
- Continuous validation replaces one-time authentication
- Micro-segmentation limits the impact of breaches
Top Endpoint Protection Software increasingly supports zero-trust implementation through improved identity integration and continuous monitoring capabilities.
Cloud-Delivered Security
Cloud-based delivery models for endpoint security offer significant advantages:
- Reduced on-premises infrastructure requirements
- Faster deployment of updates and new capabilities
- Improved scalability for growing organisations
- Enhanced threat intelligence sharing across customers
These benefits make cloud-delivered security particularly attractive for organisations seeking to modernise their security posture.
How to Select the Right Top Endpoint Protection Software for Your Business
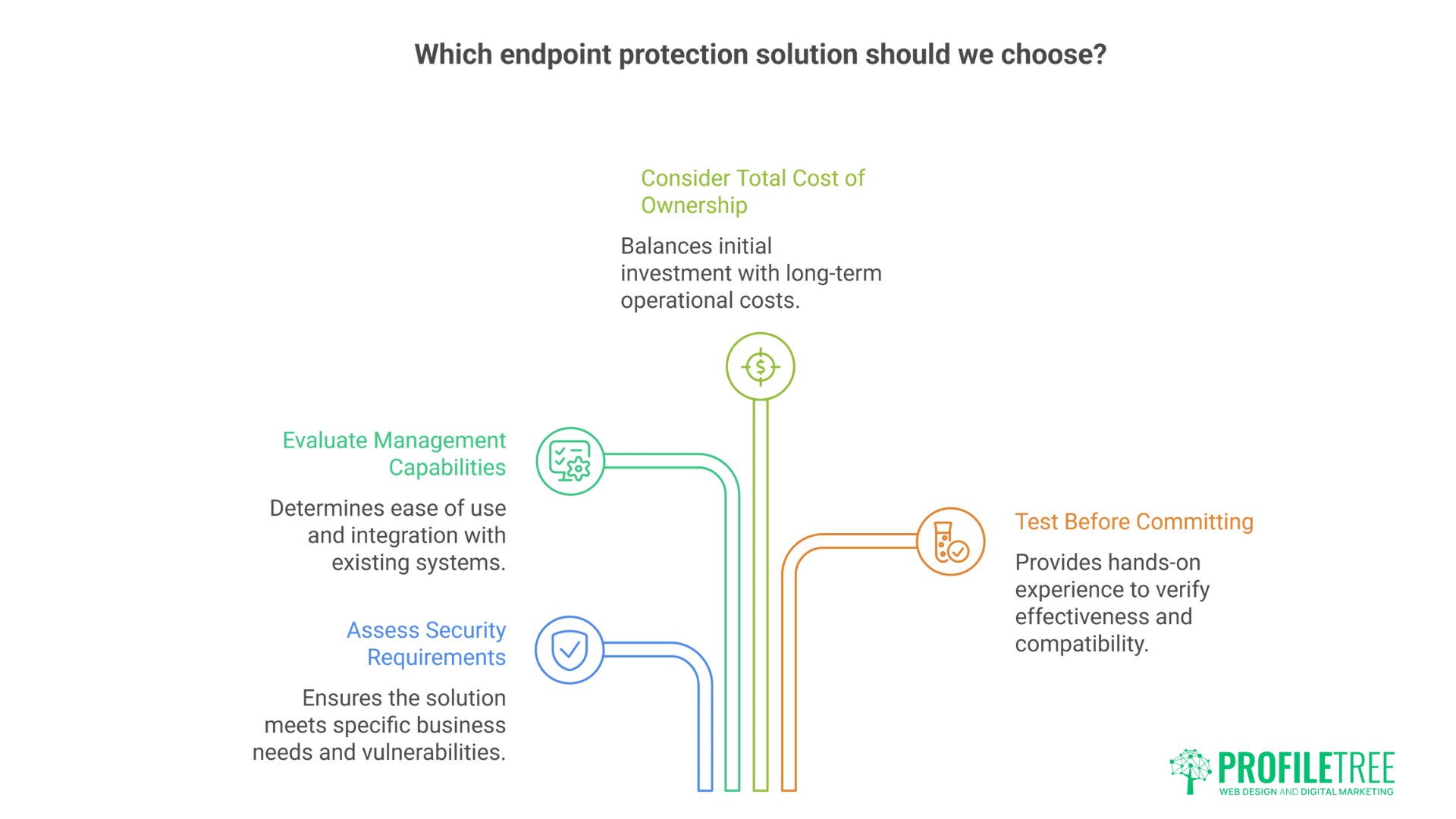
With numerous options available, selecting the most appropriate endpoint protection solution requires careful consideration of your specific business requirements.
Assess Your Security Requirements
Begin by understanding your organisation’s security needs:
- Identify your most critical assets and their protection requirements
- Document regulatory compliance obligations
- Evaluate your current security capabilities and gaps
- Consider your technical environment (operating systems, mobile devices, etc.)
This assessment forms the foundation for your selection criteria.
Evaluate Management Capabilities
Consider how the solution will fit into your operational environment:
- Assess the technical expertise available within your organisation
- Determine whether cloud-based or on-premises management is preferable
- Consider integration requirements with existing security tools
- Evaluate reporting capabilities for compliance and management purposes
The right management approach varies based on your organisational structure and resources.
Consider Total Cost of Ownership
Look beyond the initial purchase price to understand the full investment:
- Licensing costs for the expected deployment scope
- Infrastructure requirements and associated expenses
- Administrative overhead for management and maintenance
- Training requirements for security and IT personnel
A comprehensive cost analysis prevents budget surprises and helps identify the best value.
Test Before Committing
Whenever possible, test potential solutions in your environment:
- Request proof-of-concept deployments from vendors
- Evaluate performance impact on typical user systems
- Test compatibility with critical business applications
- Assess the user experience and potential productivity impacts
Practical testing often reveals considerations that aren’t apparent from feature comparisons alone.
How ProfileTree Can Help Implement Top Endpoint Protection Software
Selecting and implementing the right Top Endpoint Protection Software can be challenging, especially for businesses without dedicated security expertise. This is where ProfileTree’s digital consultancy services can provide significant value.
Security Strategy Development
Our team works with businesses across Northern Ireland, Ireland, and the UK to develop comprehensive security strategies that:
- Align with business objectives and risk tolerance
- Address specific industry compliance requirements
- Provide actionable roadmaps for security improvement
- Balance protection with operational efficiency
We help you understand not just what security measures to implement, but why they matter for your business.
Vendor Selection and Implementation Support
ProfileTree offers vendor-neutral guidance through the selection process:
- Requirements analysis and documentation
- Shortlisting of appropriate solutions
- Assistance with vendor evaluations and negotiations
- Implementation planning and project management
Our experience with diverse business environments helps identify solutions that best match your specific needs.
Security Training and Awareness
Technical solutions are only part of effective security. We help organisations develop:
- User awareness training customised to your business context
- Security policy documentation and communication
- Role-specific security guidance for administrators and users
- Ongoing education programmes to maintain security awareness
These services help ensure that human factors support rather than undermine your technical security measures.
Ongoing Security Assessment
Security is a journey, not a destination. ProfileTree offers:
- Regular security posture assessments
- Gap analysis against best practices and compliance requirements
- Remediation recommendations and prioritisation
- Guidance on emerging threats and appropriate responses
This ongoing support helps your security evolve alongside changing business needs and threat landscapes.
Call to Action: Strengthen Your Endpoint Security with ProfileTree
Cyber threats continue to evolve in sophistication and impact, making robust endpoint protection an essential component of business security. Don’t leave your organisation vulnerable to attacks that could compromise your data, operations, and reputation.
ProfileTree’s digital security consultants can help you navigate the complex landscape of Top Endpoint Protection Software to find and implement solutions that provide the protection your business needs without unnecessary complexity or cost.
Our approach combines technical expertise with business understanding, ensuring that your security investments deliver tangible benefits and address your most significant risks.
Take the first step toward stronger endpoint security by contacting ProfileTree today:
- Call us at [phone number] to speak with a security consultant
- Email [email address] to request a security assessment
- Visit our Belfast offices at the McSweeney Centre for a personal consultation
Let ProfileTree help you build a resilient security posture that protects your business assets and supports your growth objectives.
Conclusion
In an increasingly digital business environment, endpoint protection has become a fundamental requirement for organisations of all sizes. Top Endpoint Protection Software solutions provide the multi-layered defence needed to address sophisticated cyber threats and protect your valuable business assets.
The right endpoint protection approach combines technological solutions with appropriate policies, procedures, and user awareness. By considering your specific business requirements and security objectives, you can select and implement protection that provides effective security without unnecessary complexity.
Remember that security is an ongoing process rather than a one-time project. Regular assessment and adaptation are essential to maintaining protection as both your business and the threat landscape evolve.
With the right endpoint protection strategy and implementation support from ProfileTree, your organisation can achieve the security resilience needed to operate confidently in today’s challenging digital environment.